Download and install the latest Java version.
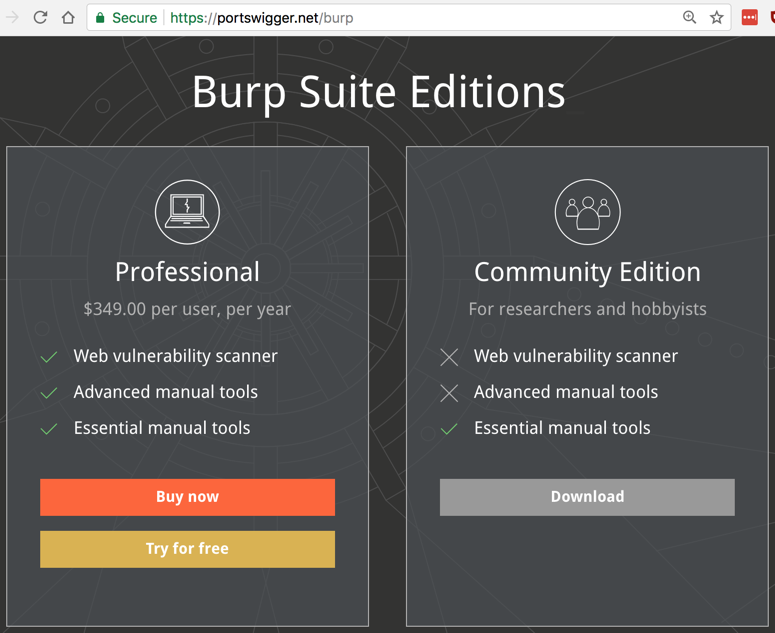
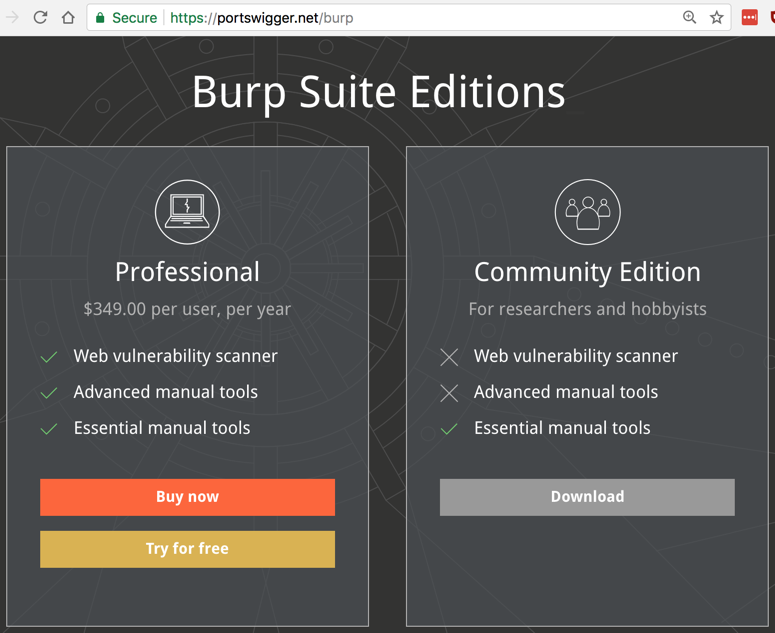
At the bottom of the "Community Edition" column, click "Download now", as shown below.
A "burpsuite_free_v1.7.03.jar" file downloads (you may have a more recent version). Double-click it to launch it.
In the first screen, accept the default selection of "Temporary project" and click Next. Click "Start Burp".
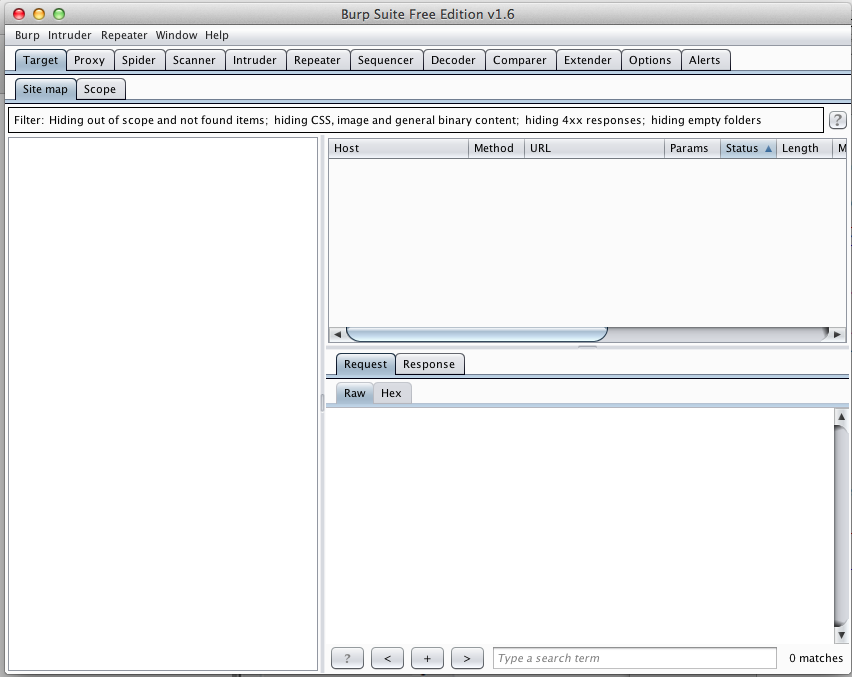
Burp opens, as shown below.
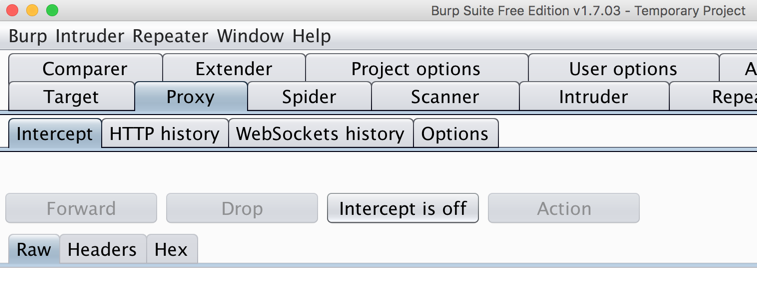
In Burp, click the Proxy tab. Click the Intercept button. If the button label reads "Intercept is on", click it to make it show "Intercept is off", as shown below.
To use Burp, you need to adjust the proxy settings on a browser on your computer. I recommend using Firefox for this purpose, so the other browsers like Chrome remain available for normal Internet use.
If you don't have Firefox, go here and get it:
Once Firefox is installed and running, in the upper right corner, click the icon with three horizontal bars, as shown below.
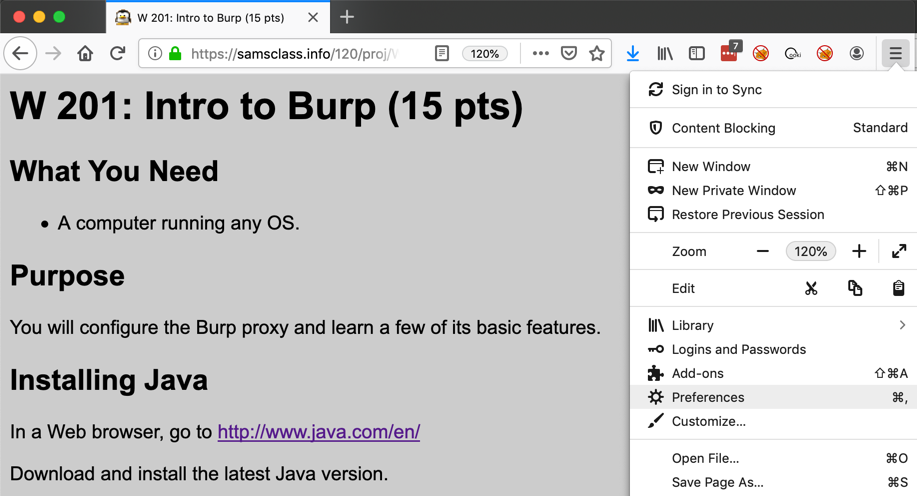
Click the gear-shaped icon. If you are using a PC, it's labeled Options. If you are using a Mac, it's labeled Preferences.
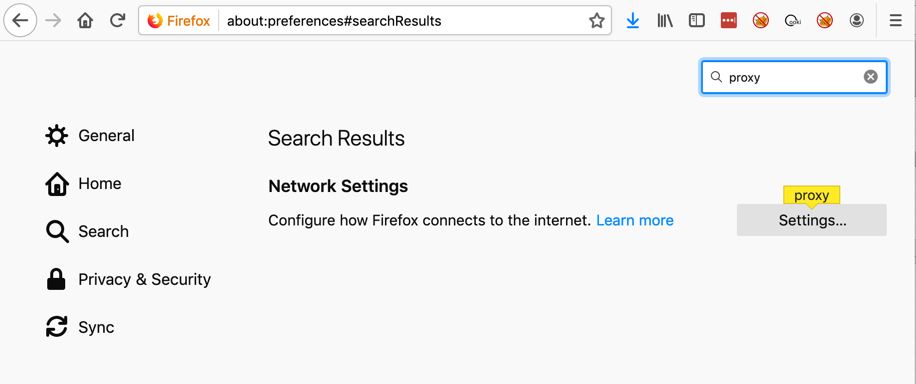
In the next page, at the top right, search for proxy, as shown below.
Click the Settings... button.
Click the "Manual proxy configuration" button and enter an HTTP Proxy address of 127.0.0.1 and a Port of 8080
Also check the "Use this proxy server for all protocols" box, as shown below.
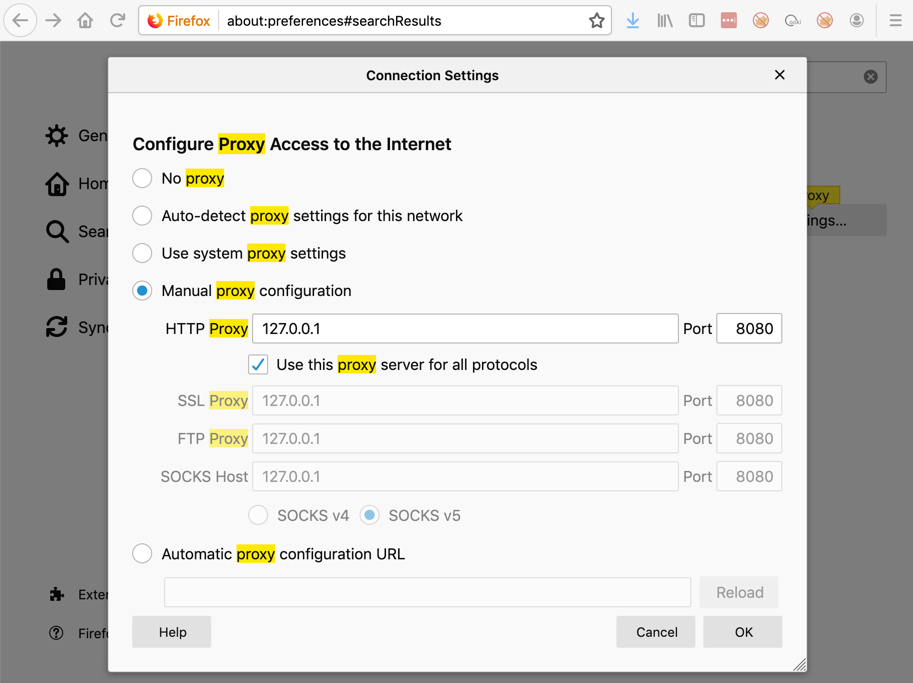
Click OK.
If you are using a PC, click OK again.
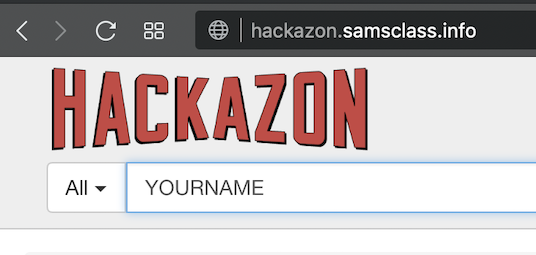
In the search bar, type your name, as shown below.
Then press Enter.
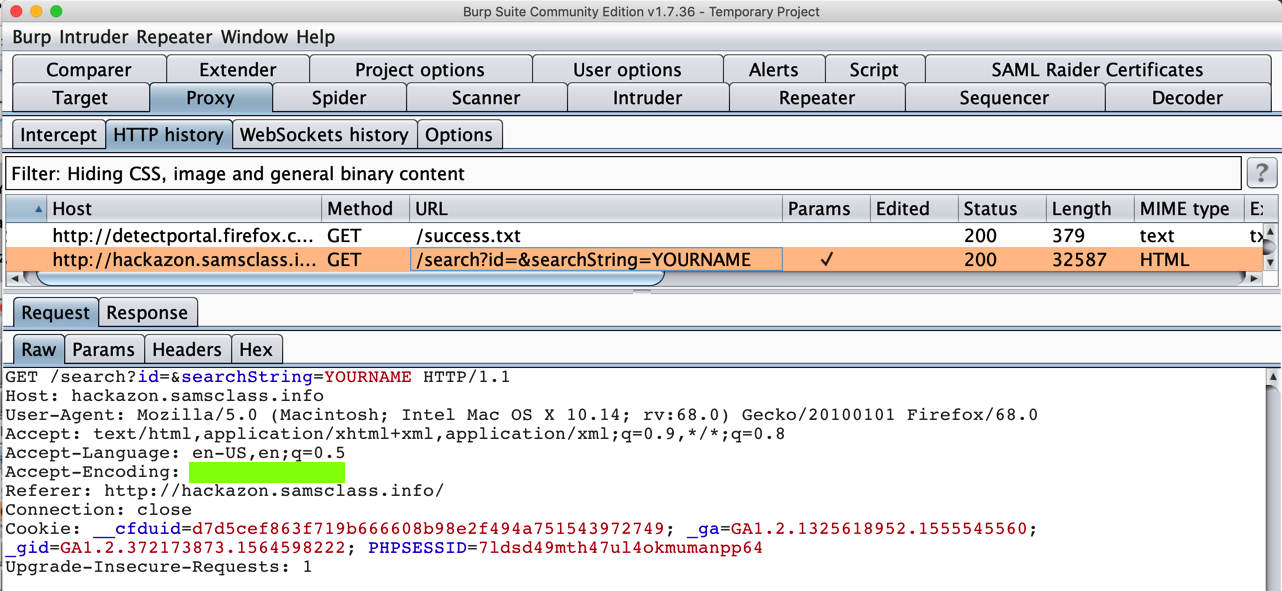
In Burp, click the Proxy tab. Click the "HTTP history" sub-tab.
Find the request to hackazon.samsclass.info containing your name, as shown below.
A certificate warning appears, as shown below, saying that the certificate came from "Portswigger", the makers of Burp, instead of a trusted Certificate Authority.
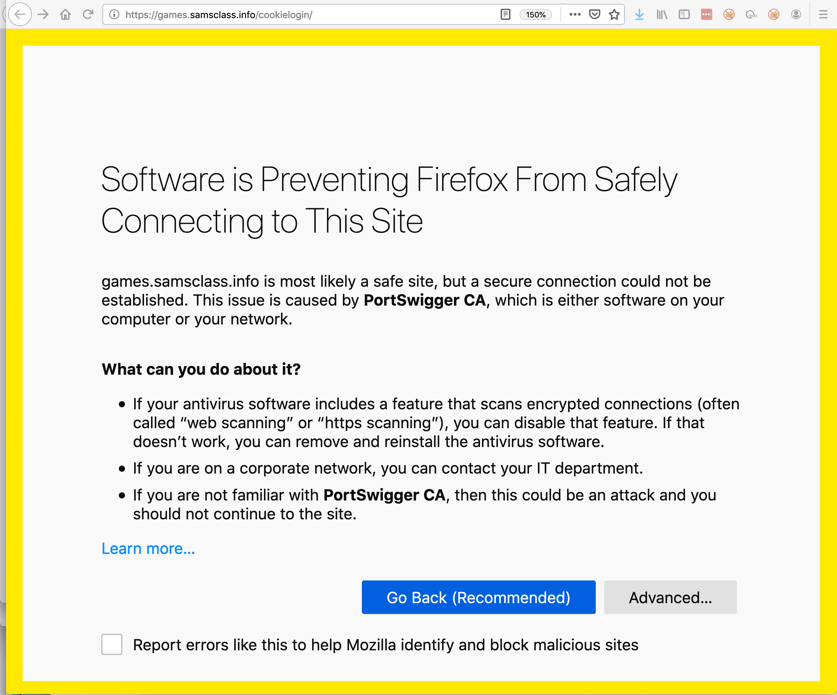
Click Advanced, "Accept the risk and continue".
Those warnings are telling you that your connection is being intercepted by a third-party (burp) which is pretending to be samsclass.info.
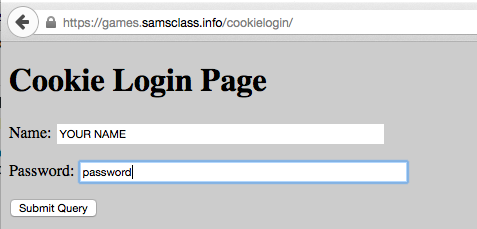
In the Cookie Login Page, type your name, as shown below.
Enter a password of password
In Burp, on the Proxy tab, click the Intercept sub-tab.
Click the "Intercept is off" button. The label changes to "Intercept is on", as shown below.
In Firefox, in the Cookie Login Page, click the "Log In" button.
In Burp, you want to capture the Burp shows the Web request shown below. If you see a different request, such as a "Detect Portal" request, click the Forward button. You may have to forward through several requests to get to the correct request.
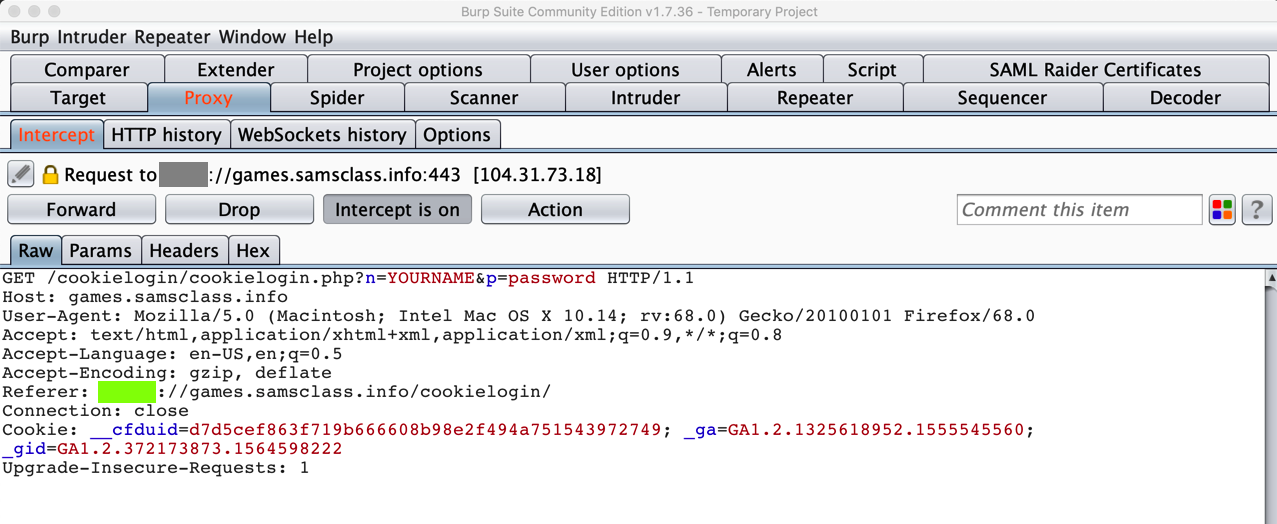
Notice that your name appears in this request, even though it's encrypted.
That's because Burp is performing a man-in-the-middle attack, acting as a Certificate Authority, delivering a fake public key instead of the genuine samsclass.info key.
Your browser warned you about this problem, but when you added the security exception you told it to proceed anyway.
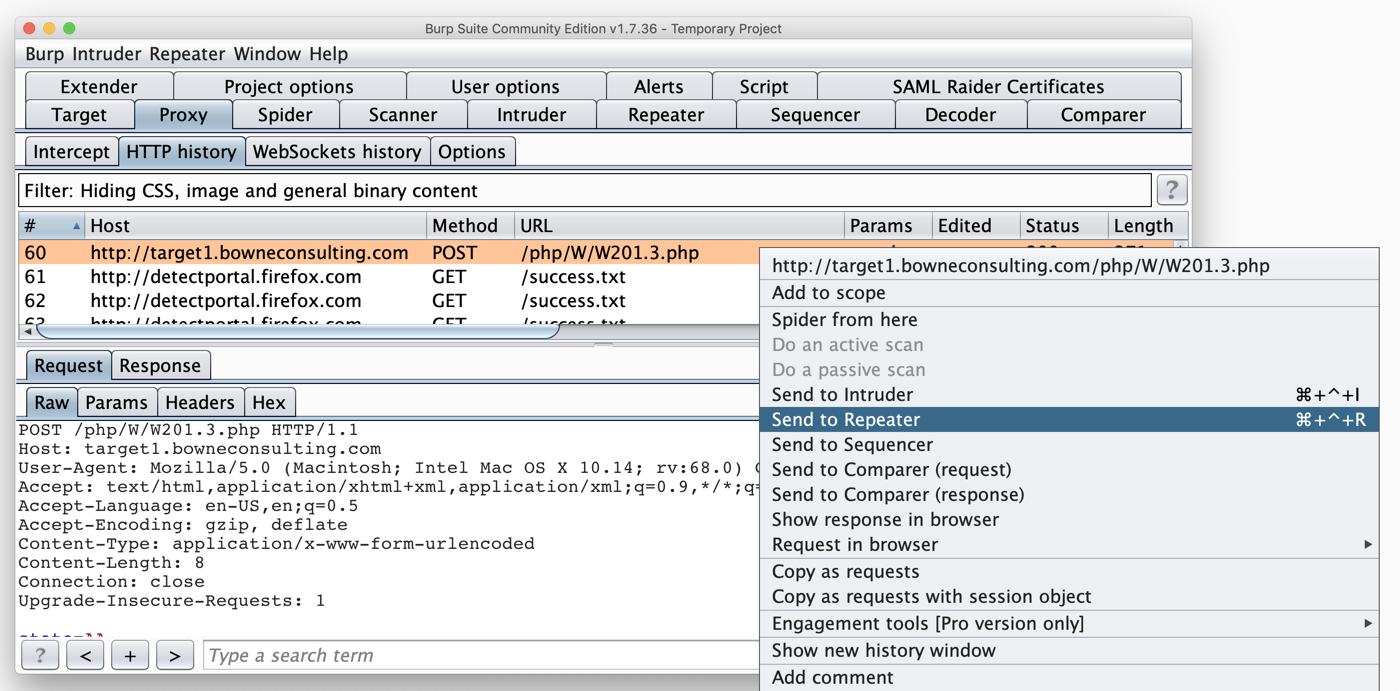
Turn off Intercept in Burp and submit a State value. Find your request in HTTP History. As shown below, right-click the request and click "Send to Repeater".
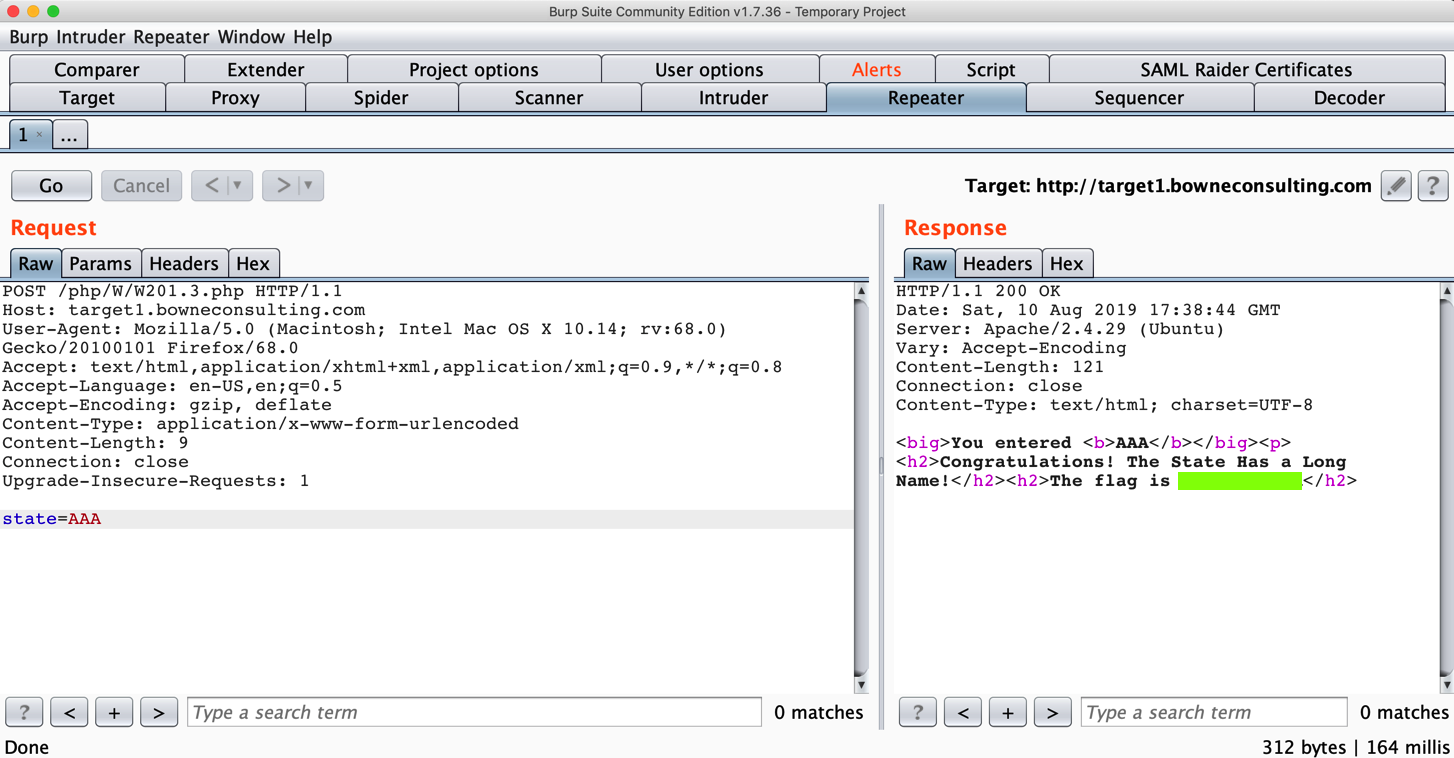
On the Repeater tab, you can edit the request as required and submit it to see the flag, as shown below.
Your goal is to buy an iPhone.
Buy an iPhone!
Buy an iPhone!
Click the gear-shaped icon.
In the Options box, at the upper right, click Advanced.
Click the Network tab.
Click the Settings button.
Click the "No proxy" button, as shown below.
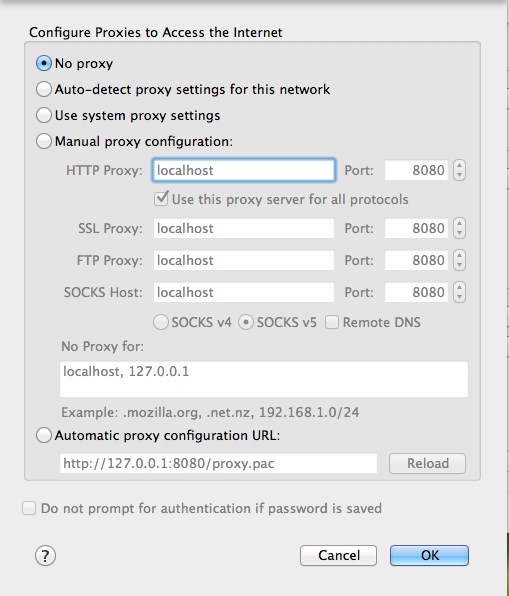
Click OK.
If you are using a PC, click OK again.