"Computer Forensics Infosec Pro Guide" by David Cowen
Publisher: McGraw-Hill Osborne Media; 1 edition (March 13, 2013)
Sold by: Amazon Digital Services, Inc.
ASIN: B00BPO7AP8
However, it contains a serious technical error, as shown below:
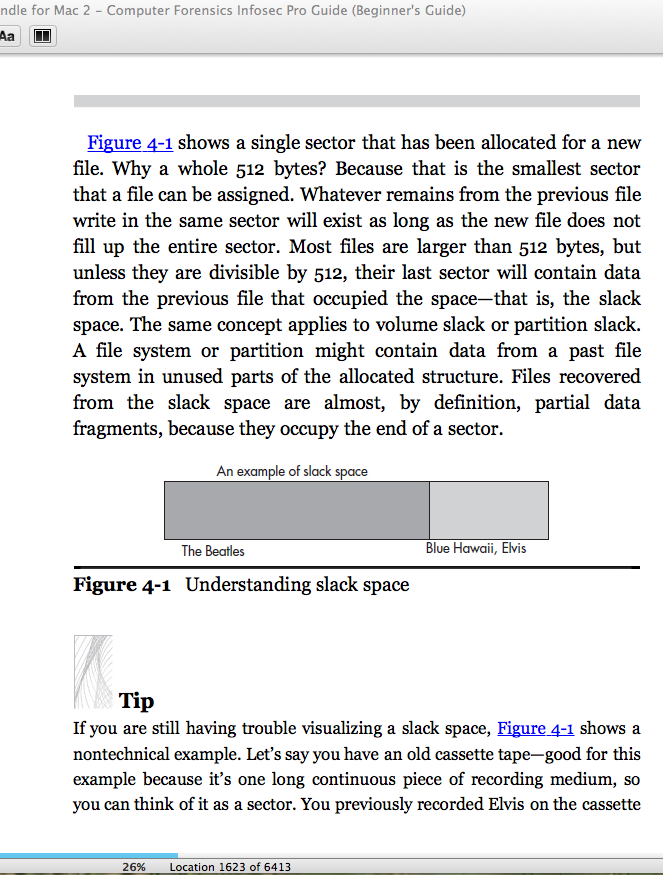
While it is of course true that data remains on a hard drive after a file is deleted, there are no residual bytes from the previous file in a 512-byte sector that is re-used.
The residual data the author is describing resides in unused sectors within a cluster that is partially filled with new data.
The data that remains in the same cluster is not from previous files at all, but from the RAM of the computer that saved the new file. This data is called RAM slack and it's always zeroes for modern operating systems, as far as I know.
This is the whole point of this hands-on project I give my forensic students:
http://samsclass.info/120/proj/p18_clusters.doc
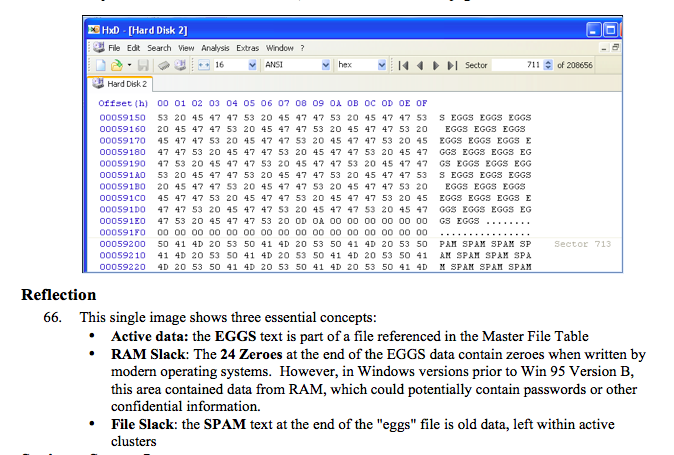
In this project, students fill a hard drive partition with large files containing SPAM, reformat the drive, and fill it again with small files containing EGGS.
Here is the result, showing the three types of data on the disk.
I plan to use the book anyway, because I can add the technical accuracy to my class through the projects, and my previous textbook made the same error.
Anyway, the fundamental rule for all computer forensics is:
TRUST NO ONE. TEST IT YOURSELF.
You cannot go to court and say "I know this because I read it in a book, or my illustrious teacher said so." You must be able to say "I know this is true, because I tested it myself."
Every book, every tool, and every teacher makes mistakes. You don't really know anything for sure until you test it yourself, hands-on.
http://www.learndfir.com/infosec-pro-guide-to-computer-forensics/
I appreciate the prompt and sensible response!
"National Center for Missing and Exploit Children" should be "National Center for Missing and Exploited Children"Loc. 1537:
The book confuses TypedURLs and Index.dat, saying:Loc. 1648:"...they were found in the Typed URLs section of the index.dat file..."However, these are two separate artifacts.Index.dat files contain Internet Explorer history, as explained here:
http://www.forensicswiki.org/wiki/Internet_Explorer_History_File_Format
TypedURLs is a registry key that contains the last 25 addresses typed into Internet Explorer, as explained here:
http://forensicartifacts.com/2010/08/typedurls/
So the text should say:
"...they were found in the Typed URLs registry key in addition to the index.dat file..."
"Elcomsoft's IOS Toolkit" should be "Elcomsoft's iOS Toolkit"
The text says: "Each of these methods will create the same forensic image..."This is not true of "Forensic imaging of live systems" -- that makes a different image than the other methods, such as "Forensic image with hardware write blockers". Live captures are important and valuable, but different from the dead images the other methods produce.
http://support.microsoft.com/kb/920730
http://forensicupdates.blogspot.com/2012/11/magnet-forensics-has-new-release.html
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileListThe path in the book is missing "SOFTWARE".
Location 4488: The Last Written Time of a user's SID-named registry key in ProfileList does not indicate the last time a user logged on, but the last time that user logged off. This is unclear in the book.
Location 4534: The UserAssist key location is incorrect. Here are the correct locations: