There should be a memdump.mem file on your Windows desktop. Drag it out of the virtual machine and drop it on the host Windows 7 machine's desktop.
When the copy finishes, close the Windows virtual machine.
Launch your Kali Linux machine. If necessary, log in as root with the password toor
Drag the memdump.mem file from your Windows 7 host machine's desktop and drop it on your Kali Linux desktop.
Note: the VMware Tools copy process is buggy and sometimes fails to copy the entire file.
You may see an error message and have to click "Retry".
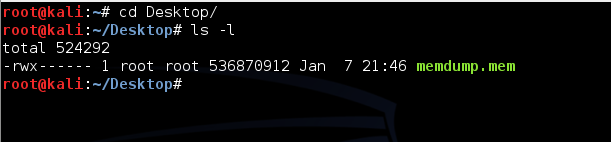
cd
cd Desktop
ls -l
You should see the memdump.mem file, which should be approximately 500 MB in size, as shown below.
In your Kali Linux machine, in a Terminal window, execute this command:
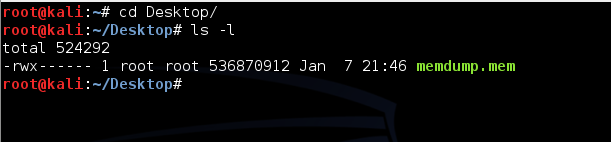
bulk_extractor -o bulk -e wordlist memdump.mem
To fix it, replace "-o bulk" with "-o bulk2".
This tells Bulk Extractor to gather data from the memdump file, put the results in a folder named "bulk", and compile a wordlist of all readable strings.
Bulk Extractor will take several minutes to run and output progress messages, as shown below:
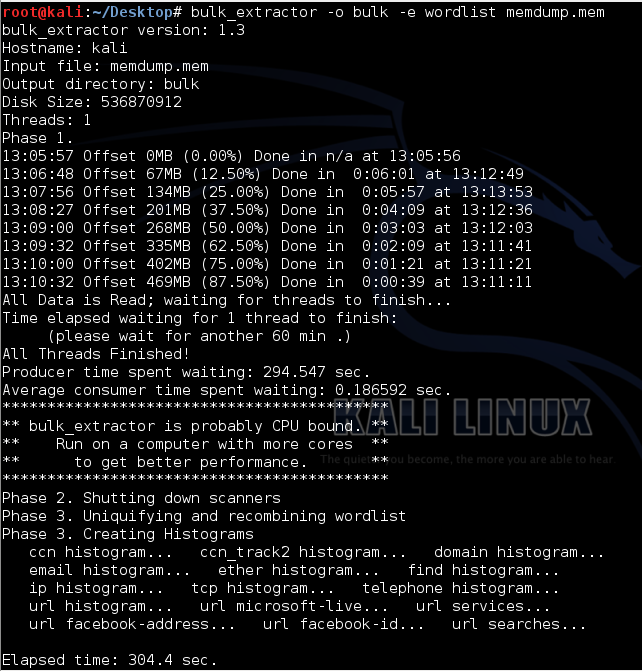
cd bulk
ls -l
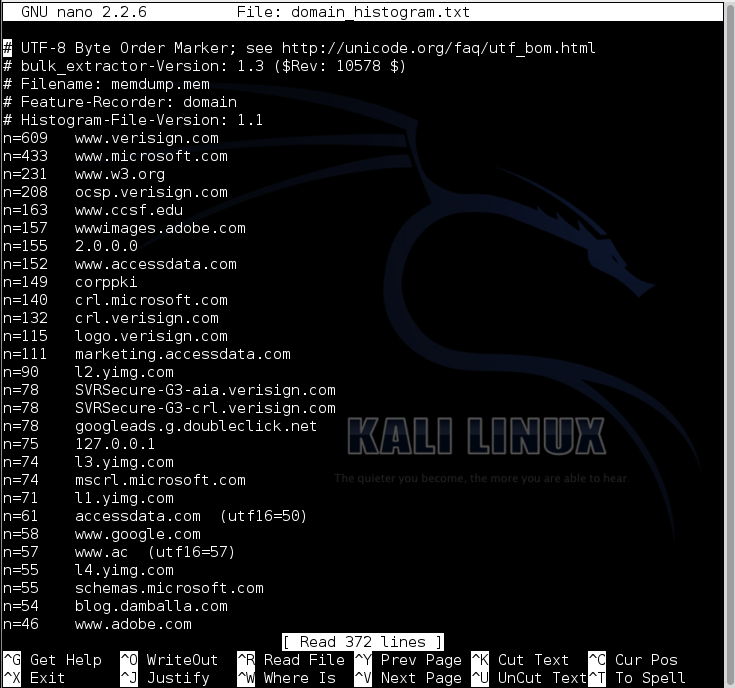
nano domain_histogram.txt
Press Ctrl+X to close nano.
nano telephone_histogram.txt
Press Ctrl+X to close nano.
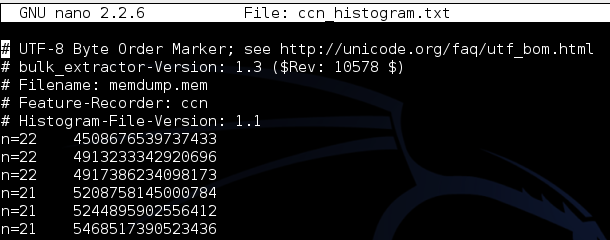
nano ccn_histogram.txt
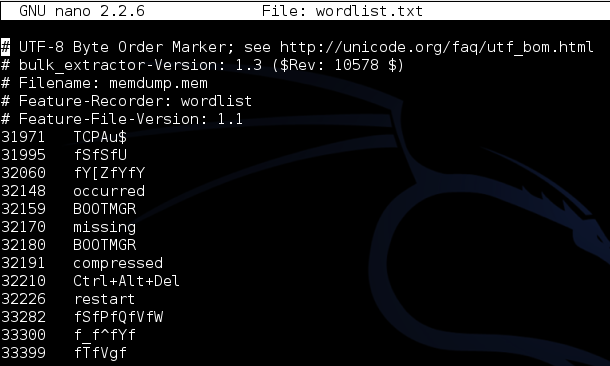
nano wordlist.txt
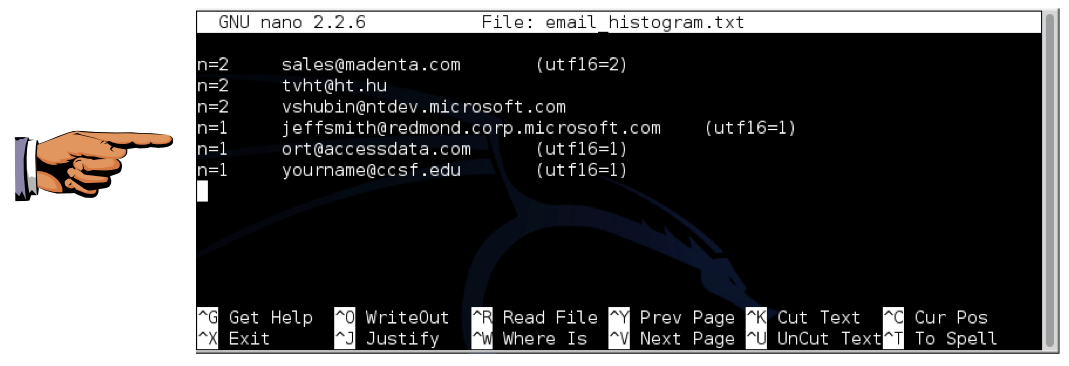
nano email_histogram.txt
Click the taskbar at the bottom of your host Windows 7 desktop, to make the host machine listen to the keyboard, instead of the virtual machine.
Press the PrintScrn key in the upper-right portion of the keyboard. That will copy the whole desktop to the clipboard.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
On the host machine, not the virtual machine, click Start.
Type mspaint into the Search box and press the Enter key.
Click in the untitled - Paint window, and press Ctrl+V on the keyboard. The desktop appears in the Paint window.
Save the document with the filename "YOUR NAME Proj 3", replacing "YOUR NAME" with your real name.
You can open the packets.pcap file in Wireshark. When I did it, most of the packets were garbled, but there were some intact NetBIOS packets.
Send a Cc to yourself.