In a Terminal window, enter this commands, and then press Enter:
ping samsclass.info
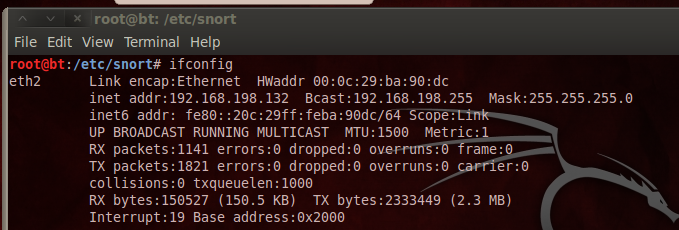
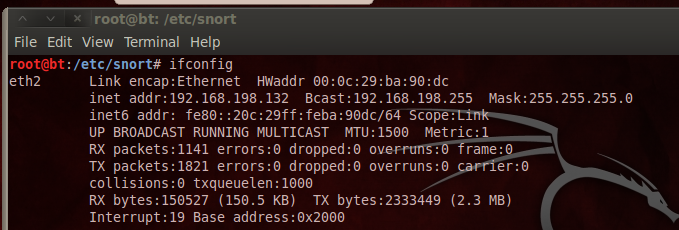
In a Terminal window, enter this commands, and then press Enter:
ifconfig
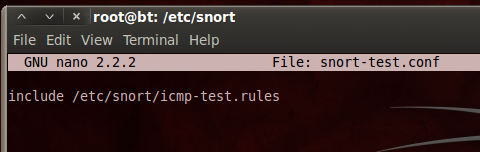
In a Terminal window, enter these commands, pressing Enter after each one:
cd /etc/snort
nano snort-test.conf
include /etc/snort/icmp-test.rules
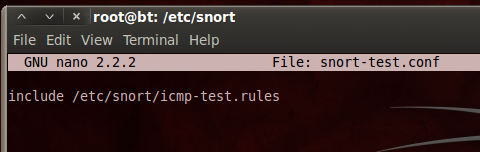
Save the file with Ctrl+X, Y, Enter.
In a Terminal window, enter these commands, pressing Enter after each one:
nano icmp-test.rules
alert icmp any any -> any any (msg:"ICMP Packet"; sid:477; rev:3;)
Save the file with Ctrl+X, Y, Enter.
This is the structure of an alert:
<Rule Actions> <Protocol> <Source IP Address> <Source Port> <Direction Operator> <Destination IP Address> <Destination > (rule options)
| Structure | Example |
|---|---|
| Rule Actions | alert |
| Protocol | icmp |
| Source IP Address | any |
| Source Port | any |
| Direction Operator | -> |
| Destination IP Address | any |
| Destination Port | any |
| (rule options) | (msg:”ICMP Packet”; sid:477; rev:3;) |
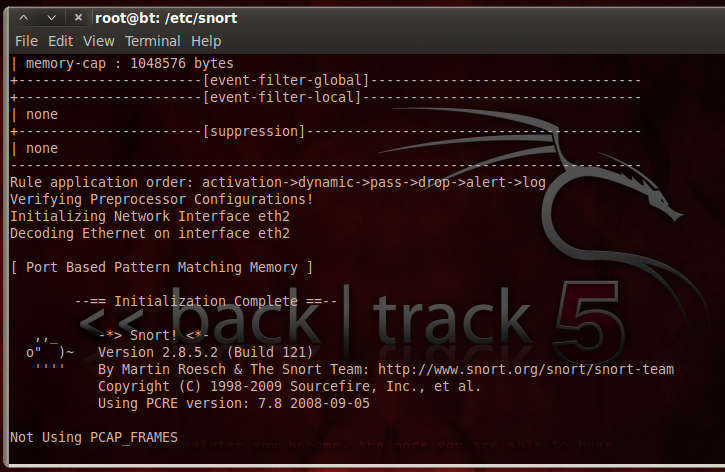
In a Terminal window, enter this command, followed by the Enter key:
snort -i eth2 -c /etc/snort/snort-test.conf -l /var/log/snort
Use your interface name, which may be different from eth2.
Snort starts, showing an "Initialization Complete" message, as shown below:
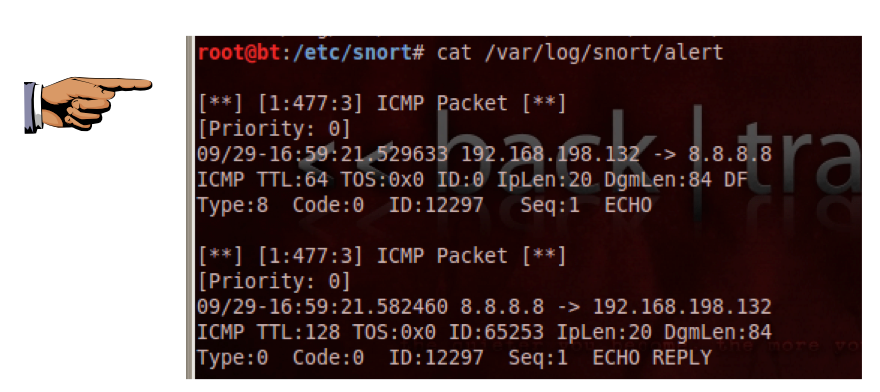
Open another Terminal window or tab and enter this command, followed by the Enter key:
ping -c 1 8.8.8.8
cat /var/log/snort/alert
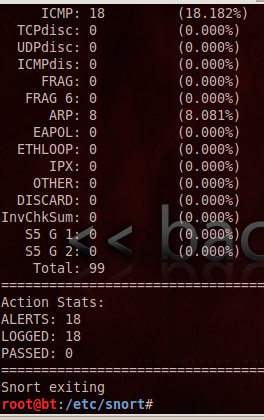
Snort prints out a page of statistics about the packets it saw, as shown below:
In a Terminal window, enter this command, followed by the Enter key:
nano /etc/snort/snort.conf
var HOME_NET.
Set this value to your subnet address, as shown below. If you are unsure what your subnet address is, open a new Terminal window or tab and execute the ifconfig command to find out.
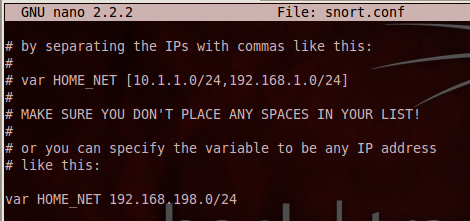
Save the file with Ctrl+X, Y, Enter.
In a Terminal window, enter this command, followed by the Enter key:
snort -i eth2 -l /var/log/snort -c /etc/snort/snort.conf
Use your interface name, which may be different from eth2.
Snort starts, showing an "Initialization Complete" message. Open another Terminal window or tab and enter this command, followed by the Enter key:
watch "tail /var/log/snort/alert"
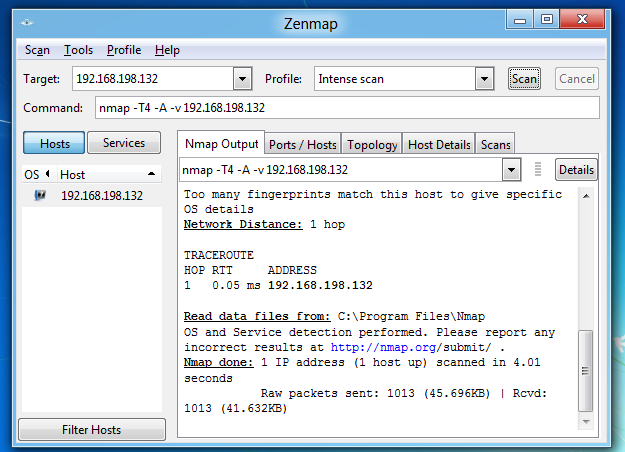
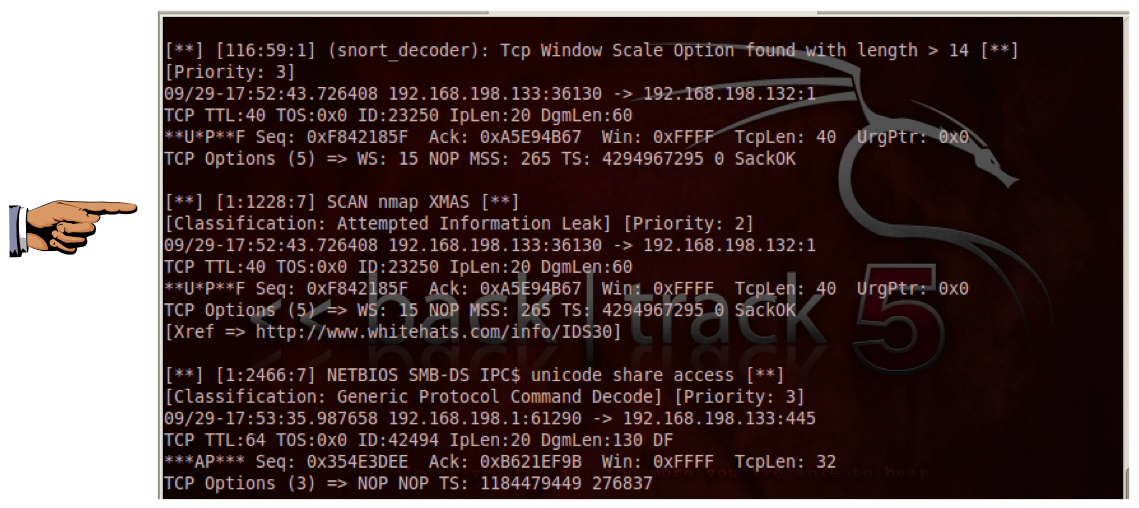
You should see messages scroll by on the Linux machine as snort sends alerts about the scans.
When the scan is complete, click in the Linux window showing the alerts, and press Ctrl+C to stop the watch command.
In a Terminal window, enter this command, followed by the Enter key:
cat /var/log/snort/alert
Email the images to cnit.122sam@gmail.com with a subject of "Project 9 from YOUR NAME".
http://people.umass.edu/cs415/labs/lab2/415-lab2-Snort.pdf
Last modified 10-4-11 6 am