If you are using some other machine, get it here:
https://samsclass.info/127/proj/putty.exe
If PuTTY won't start, right-click it, click Properties, and click Unblock.
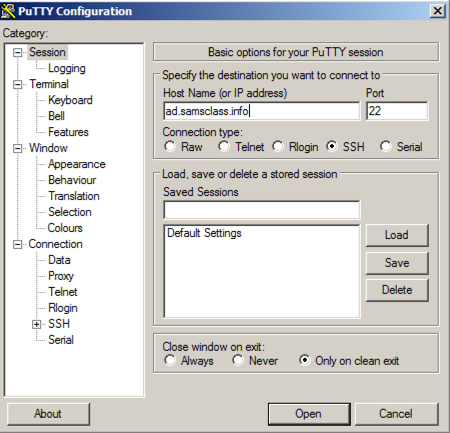
In the "Host Name (or IP address)" box, type
ad.samsclass.info
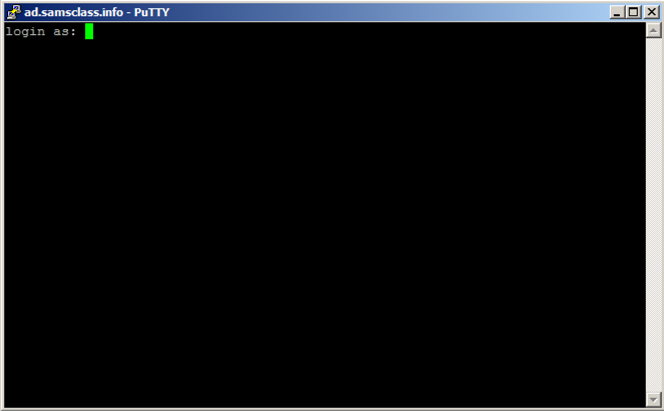
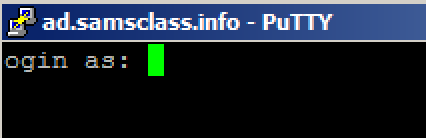
A black box opens, and shows a "login as:" prompt, as shown below.
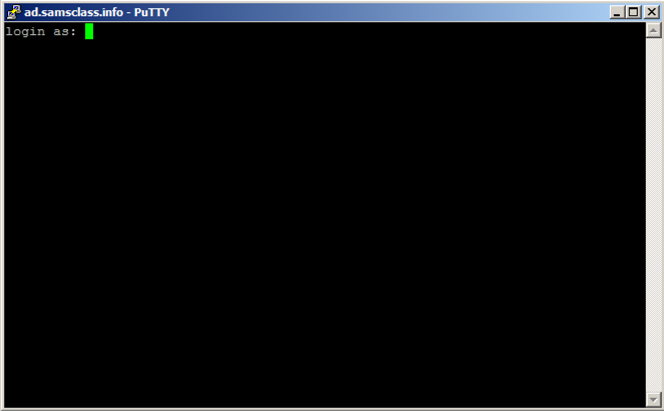
You could connect to a server at this point, but that's not the point of this project. We will alter this program to do other things instead of printing "login as".
Close the Putty window.
In Ollydbg, from the menu bar, click File, Open. Navigate to putty.exe and open it.
Ollydbg opens, as shown below. If your screen doesn't look like this, click View, CPU and maximize the CPU window.
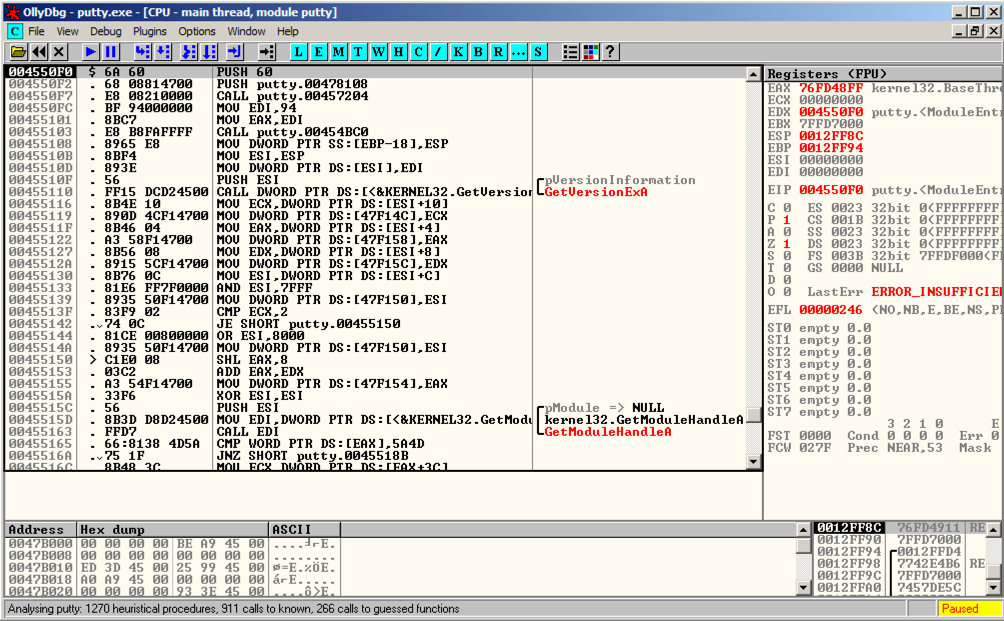
Ollydbg shows you a lot of data, but for now just notice the Assembly Code in the top left pane, and the Paused message in the lower right.
When you load a program into Ollydbg, it starts in a "Paused" state, with the Assembly Code window showing the first instruction.
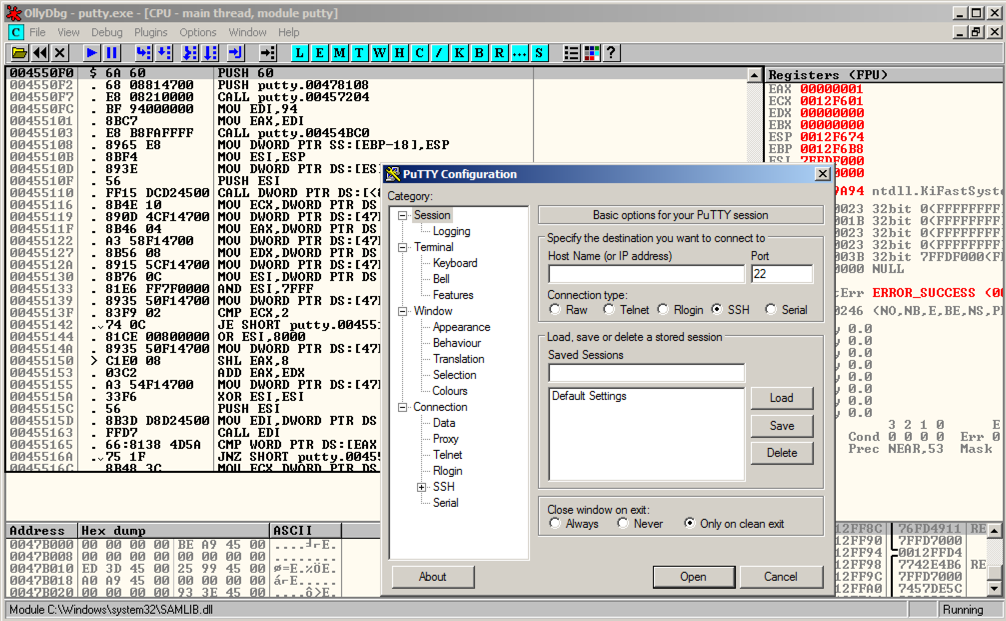
A Putty window opens, but it's behind the Olly window. At the bottom of the screen, in the taskbar, click the "PuTTY Configuration" button to bring the PuTTY window to the front, as shown below.
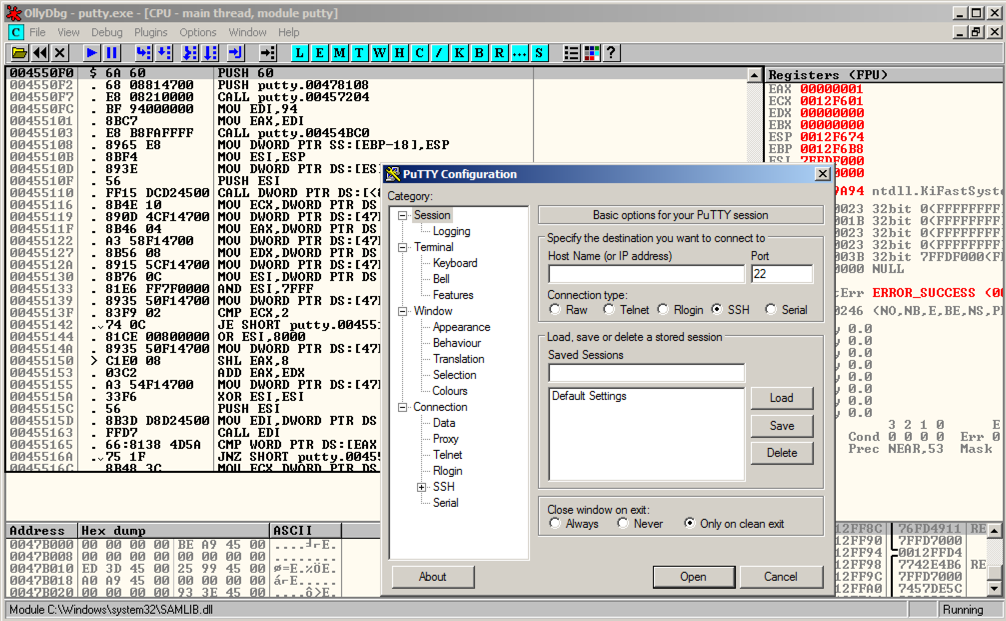
Click in the Putty window. In the "Host Name (or IP address)" box, type
ad.samsclass.info
Putty is running, but it's under the control of Ollydbg, so we can modify its execution.
In Ollydbg, from the menu bar, click Debug, Restart.
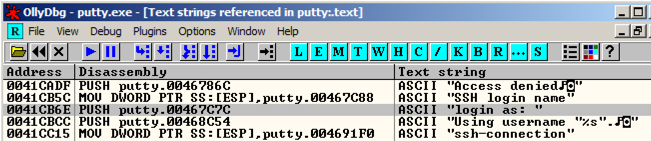
In Ollydbg, in the "Assembly Code" pane, right-click. Point to "Search for". Click "All referenced text strings", as shown below.
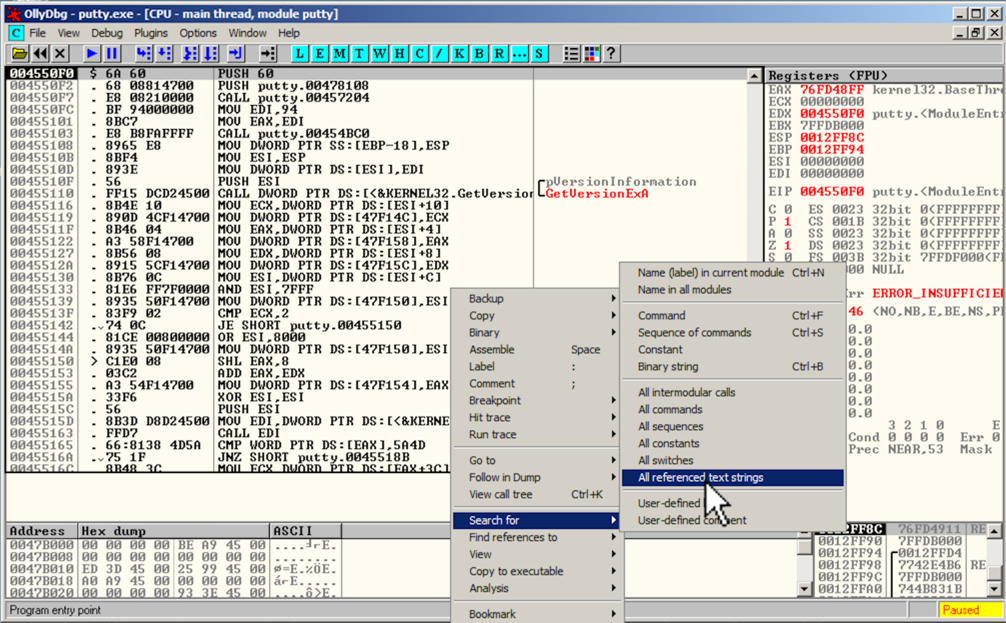
A "Text strings referenced in putty:.text" window opens, showing all the strings in the program.
To make this text easier to read, right-click, point to Appearance, Font, and click "OEM Fixed Font".
Right-click in that window, and click "Search for text", as shown below.
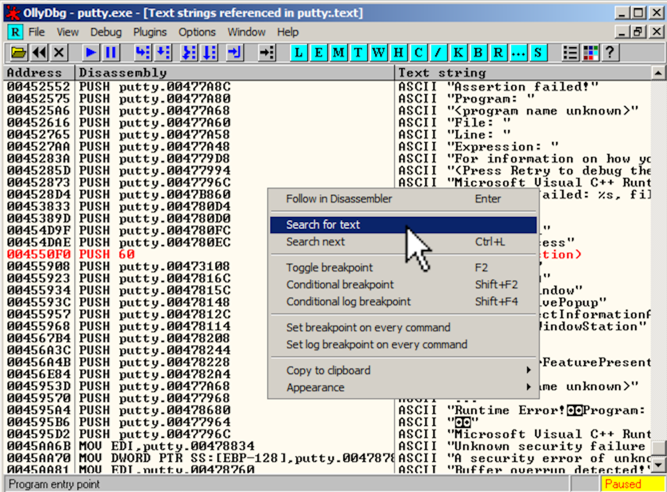
In the "Enter text to search for" box, type
login as
Click OK.
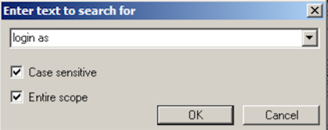
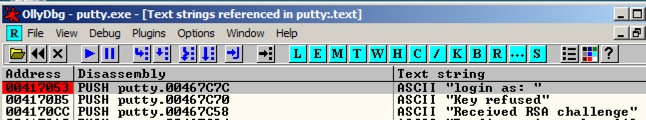
Ollydbg finds the ASCII string "login as", and the instruction that uses it, as shown below. This instruction is at address 00417053.
Right-click again, and click "Search next".
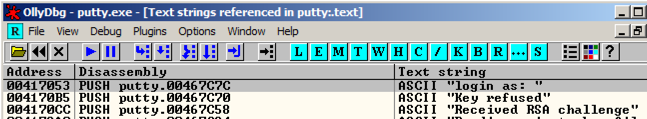
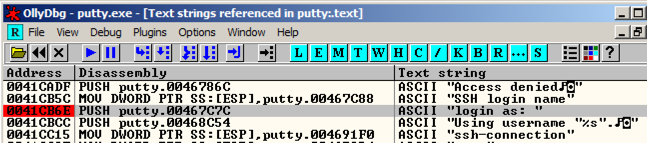
Ollydbg finds another line of code that uses this string, as shown below. This instruction is at address 0041CB6E.
Right-click again, and click "Search next".
A message appears at the bottom of the window saying "Item not found". There are only two commands in the program that use this string.
In the "Text strings referenced in putty:.text" window, right-click again, and click "Search text". In the "Enter text to search for" box, click OK.
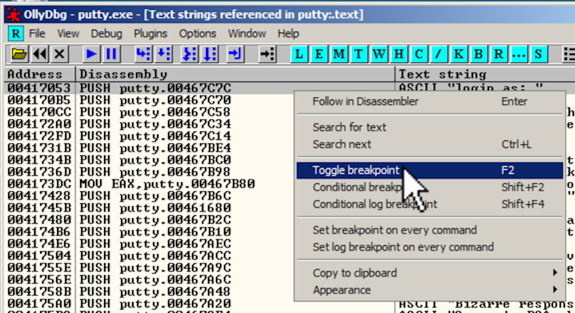
The instruction at 00417053 appears again. Right-click this instruction and click "Toggle breakpoint", as shown below.
The address turns red, as shown below, to indicate that there's a breakpoint here.
Right-click again, and click "Search next". The instruction at address 0041CB6E appears. Right-click it and click "Toggle breakpoint".
The address turns red, as shown below.
In Ollydbg, from the menu bar, click Debug, Restart.
A box pops up warning you that "Process 'putty' is active". Click Yes.
In Ollydbg, from the menu bar, click Debug, Run.
A Putty window opens. Bring it to the front, as shown below.
Click in the Putty window. In the "Host Name (or IP address)" box, type
ad.samsclass.info
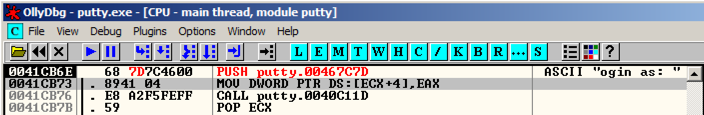
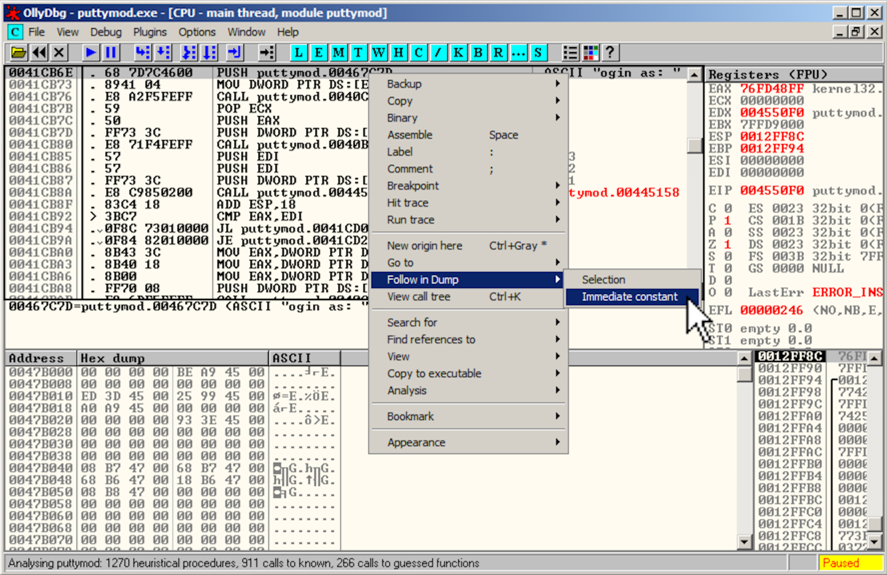
A black window opens and closes quickly, and the program stops, as shown below.
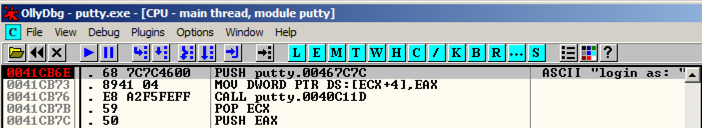
The program stopped at instruction 0041CB6E, as shown in the image above.
We'll use this instruction to hijack the program's execution.
In Ollydbg, from the menu bar, click View, Breakpoints.
A "Breakpoints" window opens, showing two breakpoints.
Right-click the first breakpoint and click Remove, as shown below.
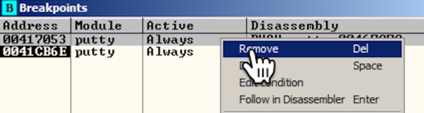
Repeat the process to remove the other breakpoint. Close the "Breakpoints" window.
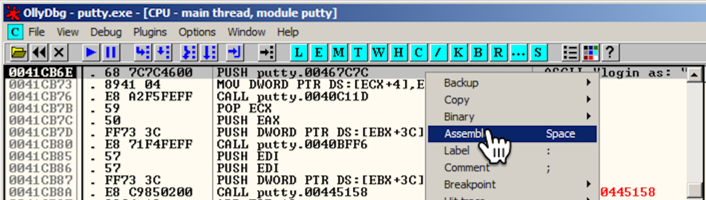
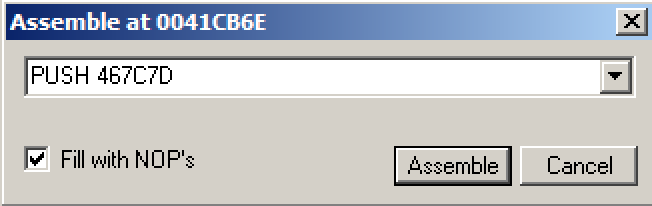
An "Assemble at 0041CB6E" box appears, as shown below.
This shows the command at this location. It's a PUSH instruction, placing the address 467C7C onto the stack. That address points to the letter "l" in the ASCII string "login as: ", as shown on the right side of the instruction line, outlined in green in the image below.
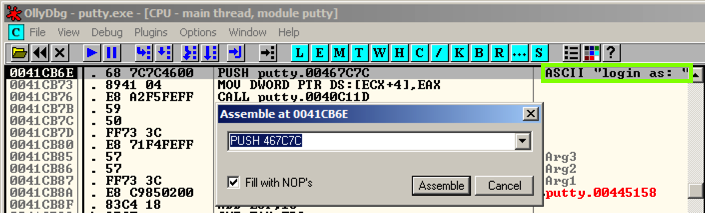
In the "Assemble at 0041CB6E" box, change the last character to D, as shown below. This will move the pointer from the "l" to the "o" in the string "login as: ".
Click the Assemble button.
Click the Cancel button.
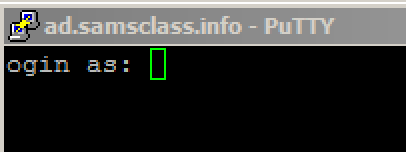
The message on the right now says "ogin as: ", as shown below.
The black login window appears, with the message "ogin as: ", as shown below.
When I did it, an error box also popped up saying "Server unexpectedly closed network connection". If that happens, just close the error box.
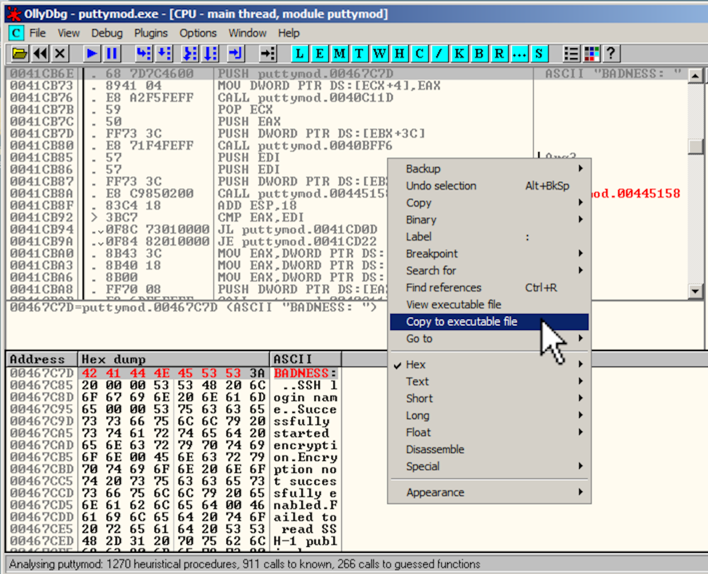
In Ollydbg, in the top left pane of the CPU window, right-click, point to "Copy to Executable", and click "All modifications", as shown below.
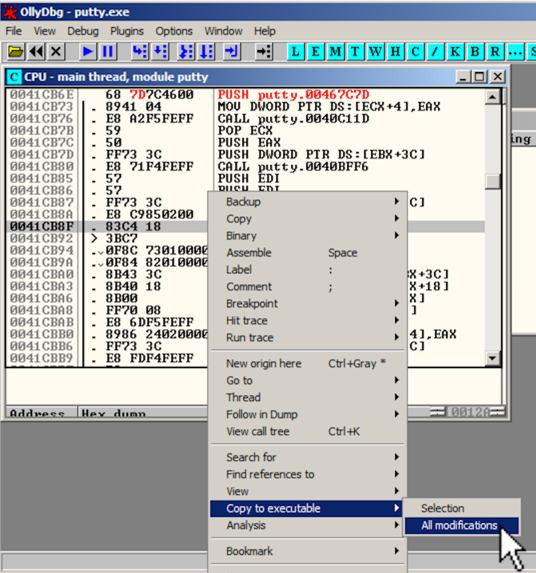
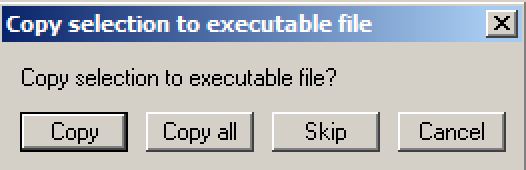
A "Copy selection to executable file" box pops up, as shown below. Click the "Copy all" button.
A new window pops up, with a title ending in "putty.exe", as shown below.
Right-click in the new window and click "Save file".
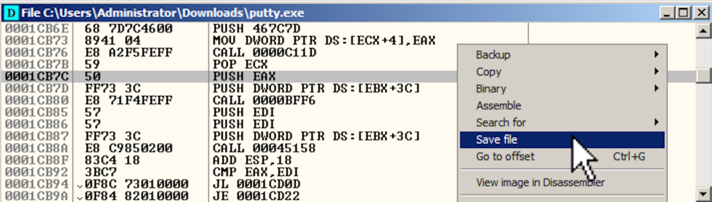
Save the file as puttymod.exe.
Double-click puttymod.exe.
In the "Host Name (or IP address)" box, type
ad.samsclass.info
A black box opens, and shows a "ogin as:" prompt, as shown below.
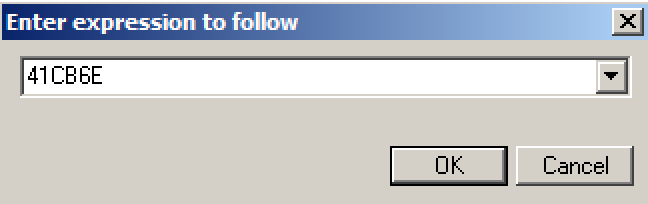
In the top left pane of the CPU window, right-click, point to "Go to", and click Expression, as shown below.
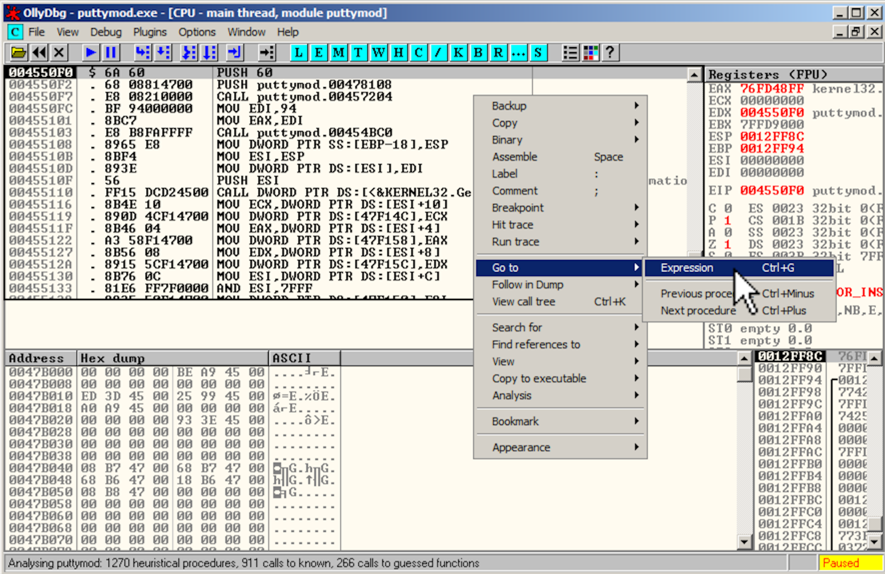
In the "Enter expression to follow" box, enter
41CB6Eas shown below. Click OK.
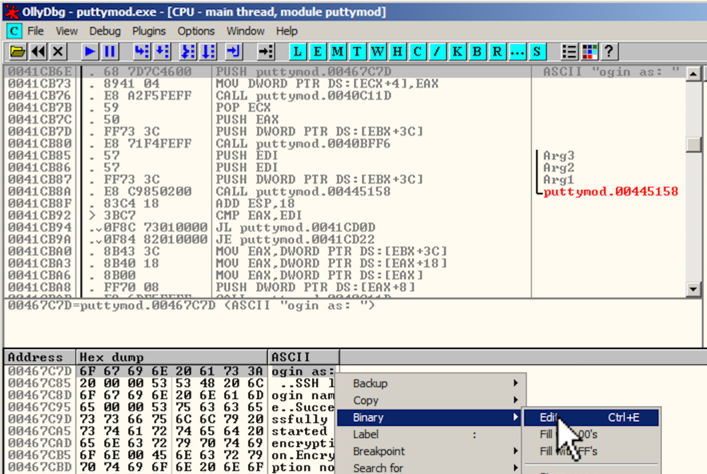
The Hex Dump pane, in the lower left, shows the text "ogin as: ", as shown below.
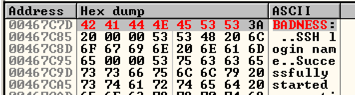
In the Hex Dump pane, highlight "ogin as:", as shown below. Right-click the highlighted text. Point to Binary. Click Edit.
An "Edit data at 00467C7D" box opens, as shown below.
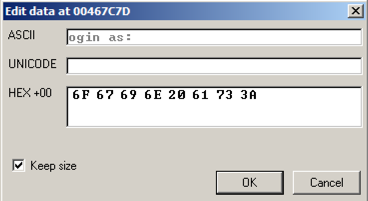
Click in the ASCII field, press Backspace to move back to the start, and overwrite the message with this text, as shown below:
BADNESS
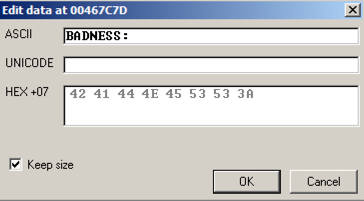
Click OK. The modified text appears in red letters in the Dump, as shown below.
A box with a long title ending in "puttymod.exe" appears showing the modified file, as shown below. Click the X in the top right of that box to close it.
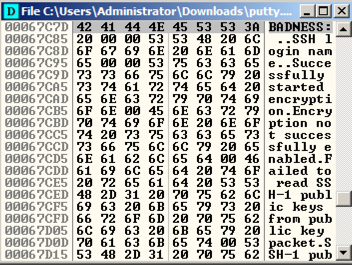
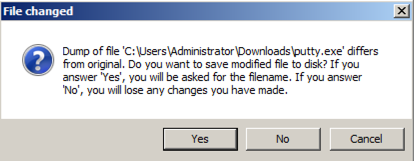
A "File changed" box appears, as shown below. Click Yes.
A "Copy selection to executable file" box pops up. Click the "Copy all" button.
A new window pops up, with a title ending in "putty.exe", as shown below.
Right-click in the new window and click "Save file".
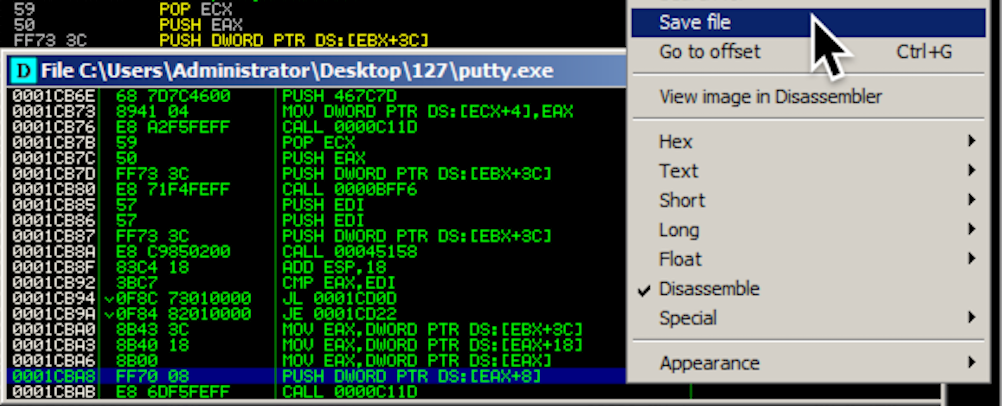
Save the file as "puttymod2.exe".
Double-click puttymod2.exe.
In the "Host Name (or IP address)" box, type
ad.samsclass.info
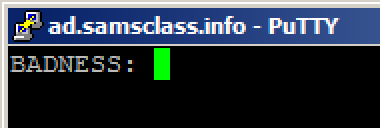
A black box opens, and shows a "BADNESS:" prompt, as shown below.
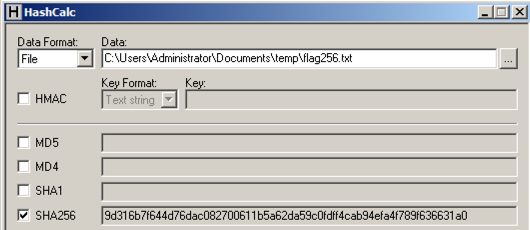
The flag is that hash like this:
07b01710
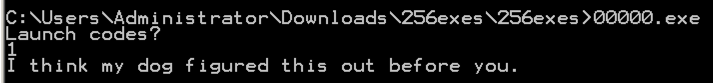
Look at the rightmost section, and you can easily see what the program does; it prints out "Launch codes?", reads in a decimal number (%d), and then chooses to print either a winning message with a result, or an insult.
The choice is performed by two instructions: CMP (Compare) and JNZ (Jump if Not Zero), outlined in green in the image below.
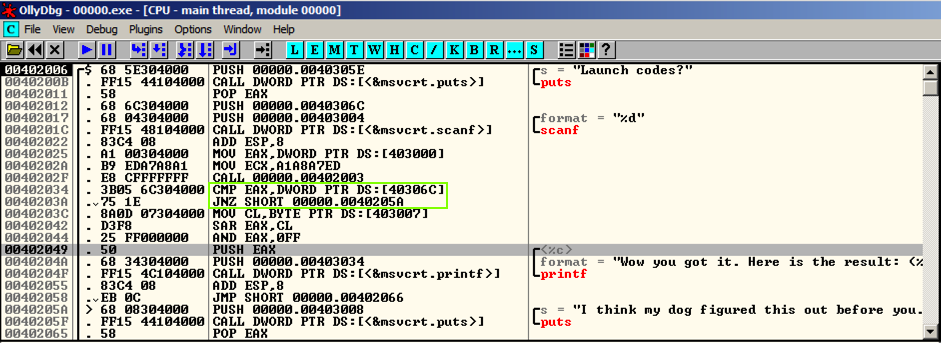
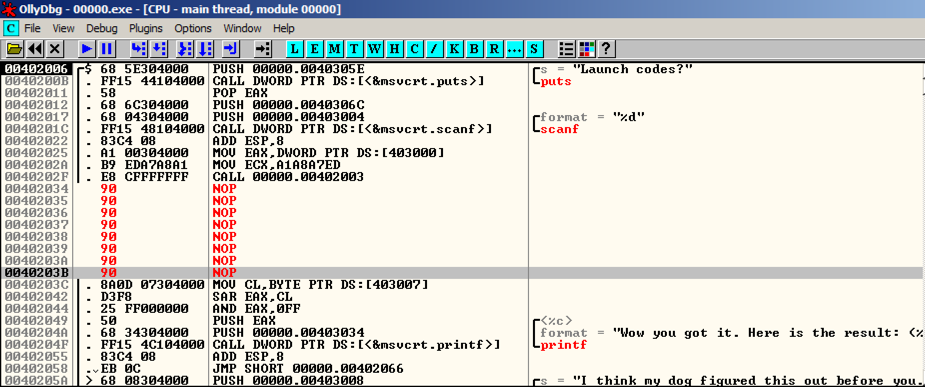
Replace those instructions with NOP (No Operation), as shown below. Save the patched file.
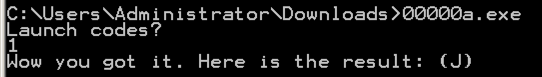

That value is the flag, like this:
07b01710
The actual results are different, of course.
CAT
Impenetrable!Cyber!
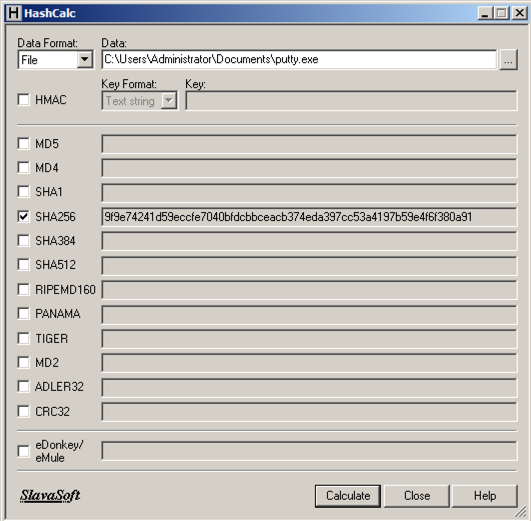
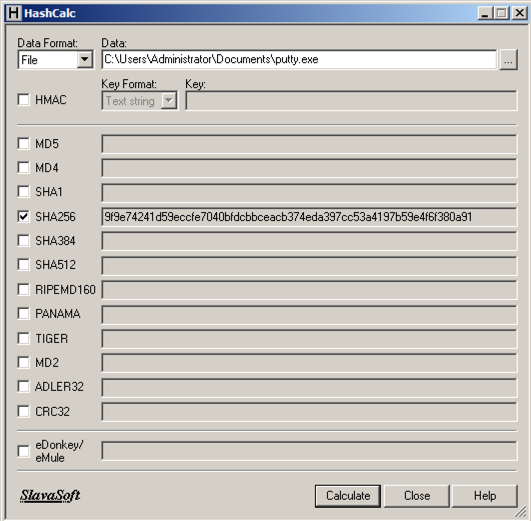
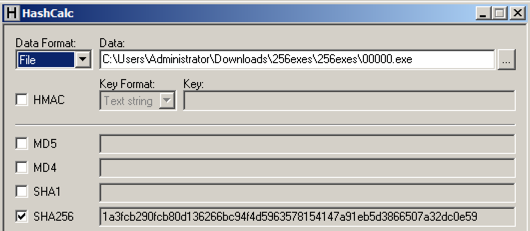
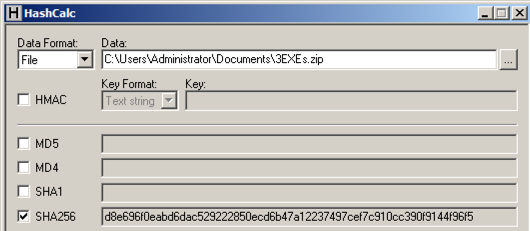
Calculate the SHA256 hash of that file. It should match the value shown below.
Calculate the CRC32 of that file to win.