Installing Python 2
This tool requires Python 2, which is not included in modern versions of Linux, like Debian 12.To install it, execute this command:
Enter your password.Paste in this text:
Save the file with Ctrl+X, Y, Enter.Then execute these commands:
git clone https://github.com/AndroBugs/AndroBugs_Framework.git
cd AndroBugs_Framework
wget https://samsclass.info/128/proj/genie.apk
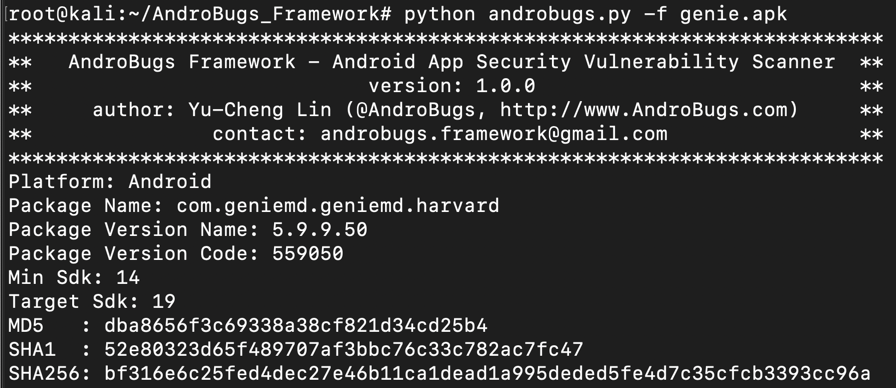
python2 androbugs.py -f genie.apk
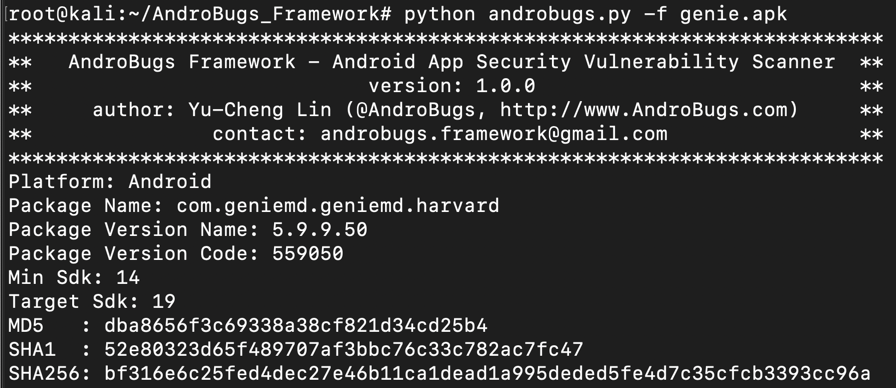
Within a minute, the scan finishes. It prints out a long report filename. Carefully copy the whole report name, which is highlighted in the image below.
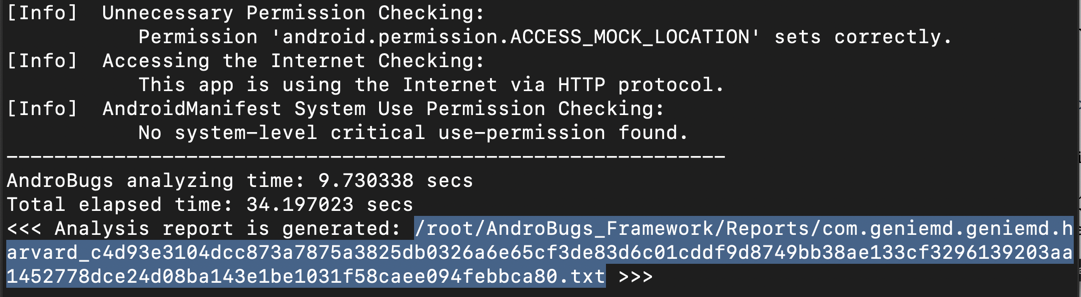
nano /root/AndroBugs_Framework/Reports/com.geniemd.geniemd.harvard_c4d93e3104dcc873a7875a3825db0326a6e65cf3de83d6c01cddf9d8749bb38ae133cf3296139203aa1452778dce24d08ba143e1be1031f58caee094febbca80.txt
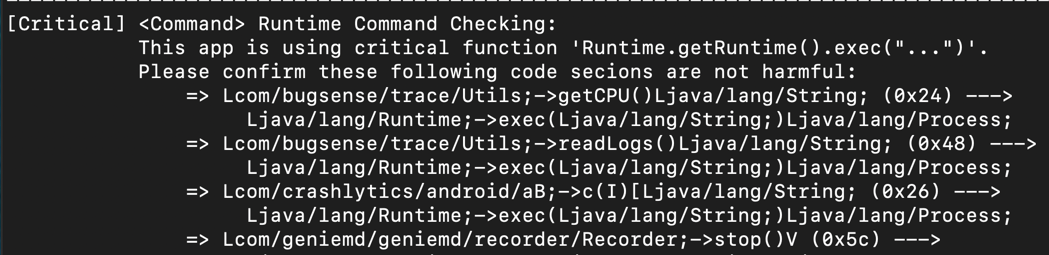
These functions use Java to construct Android shell commands, which frequently leads to command injection flaws.
M 302: SSL Validation Flaws (10 pts)
Scroll down to find the SSL validation error we exploited in a previous project. This scanner provides a lot of information about flaw, as shown below.Find the text covered by a green box in the image below. That's the flag.