At the top right, click the head icon.
Create an account, making a note of the user name and password. If you already have an account, you can use that one.
If you can't get it from the store, you can use my archived copy.
Launch the app and log in to your account.
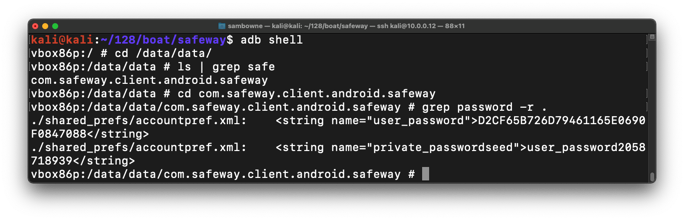
On Linux, execute these commands to find the name of the package:
adb shell
cd /data/data
ls | grep safe
cd com.safeway.client.android.safeway
grep password -r .
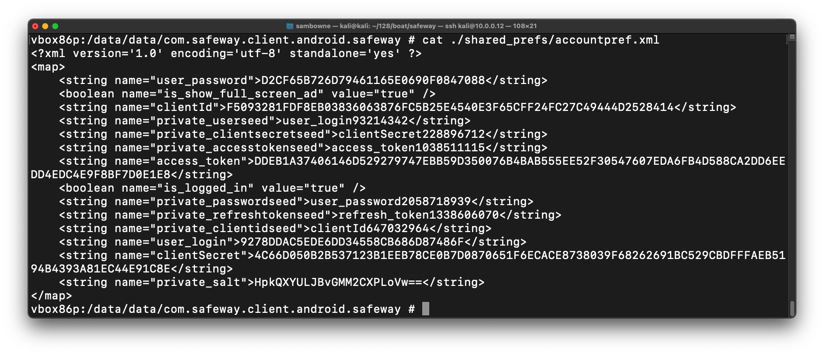
Execute this command to display the ./shared_prefs/accountpref.xml file, as shown below.
cat ./shared_prefs/accountpref.xml
Copy this data into a text file so you can use it later.
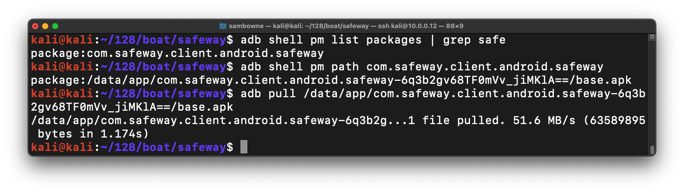
On Linux, execute this command to find the name of the package:
adb shell pm list packages | grep safe
adb shell pm path com.safeway.client.android.safeway
adb pull /data/app/com.safeway.client.android.safeway-6q3b2gv68TF0mVv_jiMKlA==/base.apk
sudo apt update
sudo apt install jadx
jadx-gui
If you get "Hash Sum mismatch" errors, try these solutions:
In jadx-gui, open the APK file you downloaded. In the left pane, expand these items:Source codeClick DataEncryptionUtil and scroll down to see the getRawKey method, as shown below.
com
safeway
client.android
util
M 404.1: Word (10 pts)
The flag is the word covered by a green rectangle in the image below.
That's easy to reverse in Python, and all the values you need are in the accountpref.xml file.
On Linux, execute these commands:
sudo apt update
sudo apt install python-pip -y
python2 -m pip install pycryptodome
nano safeway.py
from Crypto.Cipher import AES
from Crypto.Protocol.KDF import PBKDF2
private_passwordseed = 'user_password2058718939'
private_salt = 'HpkQXYULJBvGMM2CXPLoVw=='
user_password = 'D2CF65B726D79461165E0690F0847088'
seed = private_passwordseed
salt = private_salt.decode("Base64")
secret_key = PBKDF2(seed, salt).encode("hex")
secret_key = secret_key.decode("hex")
iv = private_passwordseed[::-1]
n = len(iv)
iv = iv[n-16:n]
ciphertext = user_password.decode("hex")
cipher = AES.new(secret_key, AES.MODE_CBC, iv)
print "Password: ", cipher.decrypt(ciphertext)
Execute this command to run the program:
python2 safeway.py
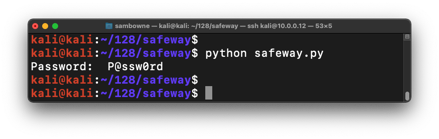
Replace the private_passwordseed, private_salt, and user_password values with the ones you copied earlier from your Android phone and run the program again. You should see your own password.
Posted 2-12-21
M 404.2: Password (10 pts)
Find the password encoded in the data below. That's the flag.<?xml version='1.0' encoding='utf-8' standalone='yes' ?> <map> <string name="user_password">2EAF39B8313BA08B9401A6215DFB613D</string> <boolean name="is_show_full_screen_ad" value="true" /> <string name="clientId">F609C028E52189D3039317C96C31528429E726FCF7B98BC96D3C6C877913F682</string> <string name="private_userseed">user_login93214342</string> <string name="private_clientsecretseed">clientSecret228896712</string> <string name="private_accesstokenseed">access_token891623486</string> <string name="access_token">AE96B0ADE0B14240F9E52647C766EA64E478CD223399A0B4B1900EBF4F53785BB3BF6BE2E1E0C44EC4D1600992547D66</string> <string name="private_passwordseed">user_password855751249</string> <boolean name="is_logged_in" value="true" /> <string name="private_refreshtokenseed">refresh_token720082475</string> <string name="private_clientidseed">clientId647032964</string> <string name="user_login">7F3FC74FB413BC0C74F8CB9C29523AF9</string> <string name="clientSecret">FA0B4FC1B2732B2B2EB82A13F8135FBB76D43458158783A782506D0DE02EFE65E1F61848431F9876F759EF04161B0862</string> <string name="private_salt">wUJQTtm3Msc3bBHpDwuT9w==</string> </map>