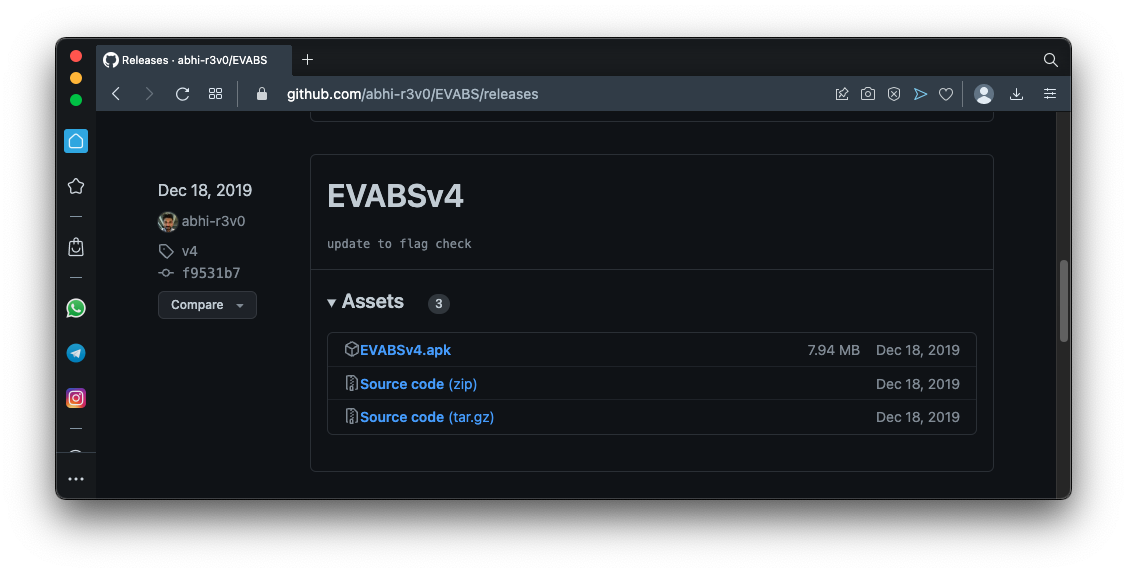
On your host system, in a Web browser, go to
https://github.com/abhi-r3v0/EVABS/releases
Download EVABSv4.apk, as shown below.If that page is not available, use this alternate link.
Drag the EVABSv4.apk file and drop it on your running Android emulator.
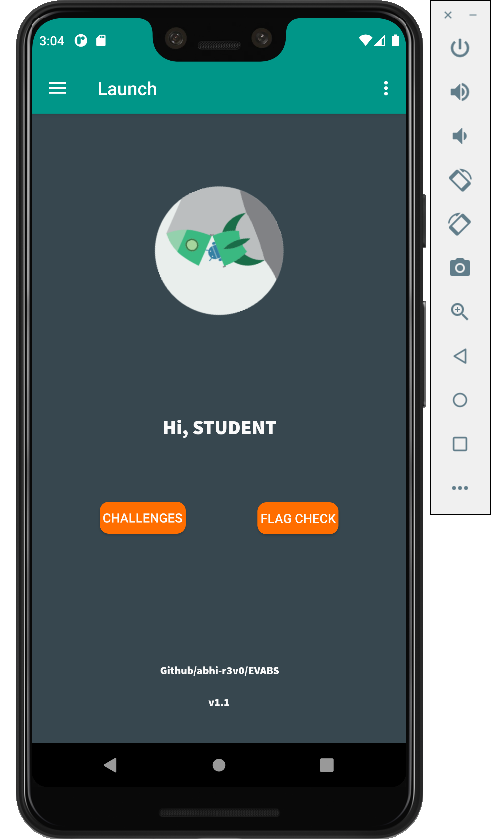
On the second page, enter your name and click ACCESS.
The main page opens, as shown below.
Click CHALLENGES.
Read the instructions and the hint on this page to understand the challenge, as shown below.
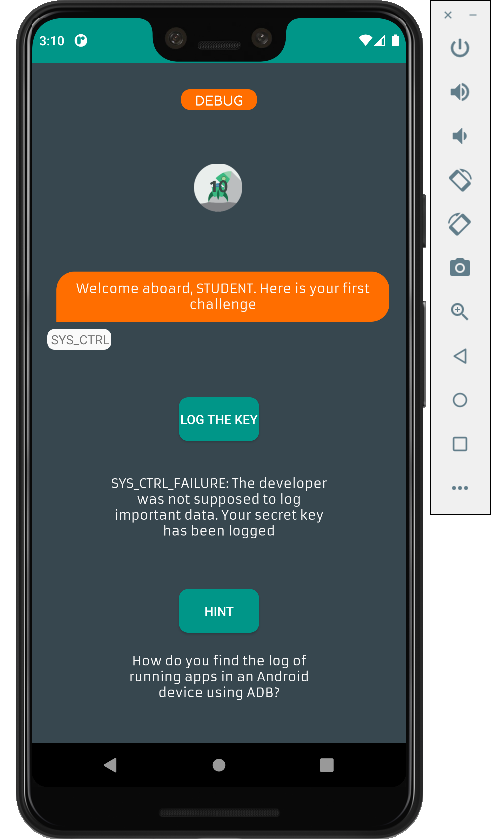
Connect to your Android device with adb and use this command to monitor the log:
./adb logcat
M 512.1: LEVEL 1: Debug Me (5 pts)
In EVABS, click the "LOG THE KEY" button. The key appears in the log, as shown below.The flag is covered by a green rectangle in the image below.
M 512.2: LEVEL 2: File Access (5 pts)
Unpack the APK file with apktool.Look in the "assets" folder. The flag is easy to find.
M 512.3: LEVEL 3: Strings (5 pts)
In the unpacked APK, look in the "res/values/strings.xml" file.
M 512.4: LEVEL 4: Resources (5 pts)
Unpack the APK file with apktool.Look in the "res/raw/link.txt" file. The flag is easy to find.
M 512.5: LEVEL 5: Shares and Preferences (5 pts)
You need to root your emulator first, as explained in project M 412.Execute these commands to look in the shared_prefs:
Examine the files in that folder with the cat command to find the flag.
M 512.6: LEVEL 6: DB Leak (5 pts)
Click the "FETCH CREDS" button.Execute these commands to look in the database:
Examine the files in that folder with the cat command to find the flag.
M 512.7: LEVEL 7: Export (5 pts)
In the unpacked APK file, examine the AndroidManifest.xml file.On the fourth line, an exported activity is defined, as shown below:
<activity android:exported="true" android:name="com.revo.evabs.ExportedActivity"/>Execute these commands to launch that activity:The flag appears on your emulator, as shown below.
M 512.8: LEVEL 8: Decode (5 pts)
Open the APK in jadx-gui, as you did in project M 402.Open the Debug class, as shown below.
Decode the three strings shown in red from Base64 to see the flag.
Note: A student using jadx-gui version 1.45 saw these three strings mingled together. Version 1.44 shows them as shown below.
M 512.9: LEVEL 9: Smali injection (15 pts)
In jadx-gui, examine the SmaliInject class. Find the code highlighted in the image below. This will print the flag if the signal is "LAB_ON".
In the unpacked APK, edit this file:
./smali/com/revo/evabs/SmaliInject$2.smaliNote: to refer to that file from the Bash command line, you need to add a backslash before the dollar-sign.Comment out the "if-eqz" line highlighted in the image below.
This will make it always print the flag.
Repack and sign the APK as you did in project M 401.
On your emulator, uninstall the original EVABS app.
Install the modified app.
Open Level 9. Click the "TURN ON" button. The flag appears, as shown below.
M 512.10: LEVEL 10: Intercept
Skip this one, it's broken. The website it connects to is gone.
M 512.11: LEVEL 11: Custom Access
This challenge needs Frida to do, I haven't written instructions for that yet.
M 512.12: LEVEL 12: Instrument
This challenge needs Frida to do, I haven't written instructions for that yet.