This project only finds the local storage flaw in the Android app.
I tested several other apps from that developer and found that they all had similar flaws. I notified the developer on 1-7-17 and got no response.
I see no reason to bother notifying them again about the iOS vulnerabilities--it's obvious that they don't care.
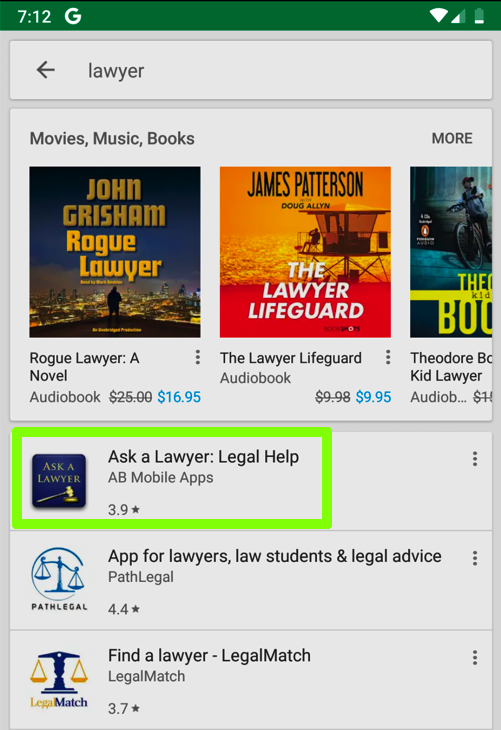
Register an account with the password
topsecret3-YOURNAME
Relace "YOURNAME" with a version of your name that doesn't contain any spaces.

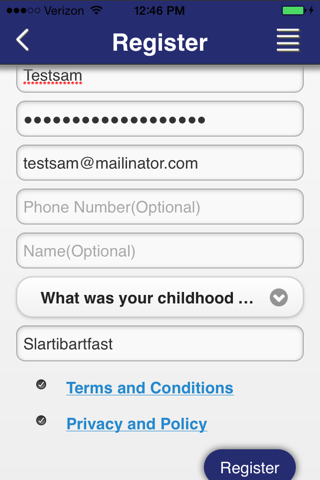
adb connect 172.16.123.154
adb devices -l
adb shell
On Kali, in the Terminal, execute these commands:
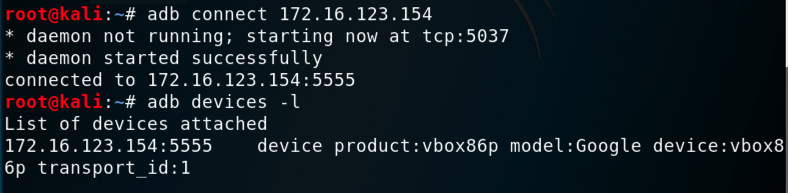
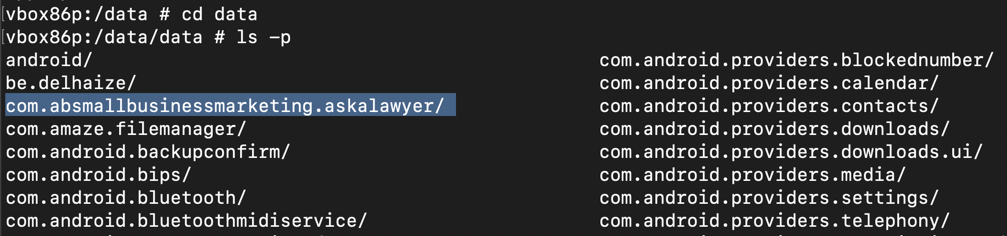
cd data
ls -p

On Kali, in the Terminal, execute these commands:
cd data
ls -p
Each app has its own directory here. Most of them begin with "com.android" because they are part of the Android operating system, but near the top, you see the com.absmallbusinessmarketing.askalawyer/ directory, highlighted in the image below.
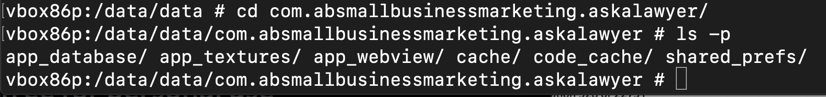
On Kali, in the Terminal, execute these commands:
cd com.absmallbusinessmarketing.askalawyer
ls -p
This is where the "Ask a Lawyer" app stores its local data.
grep pass . -ra
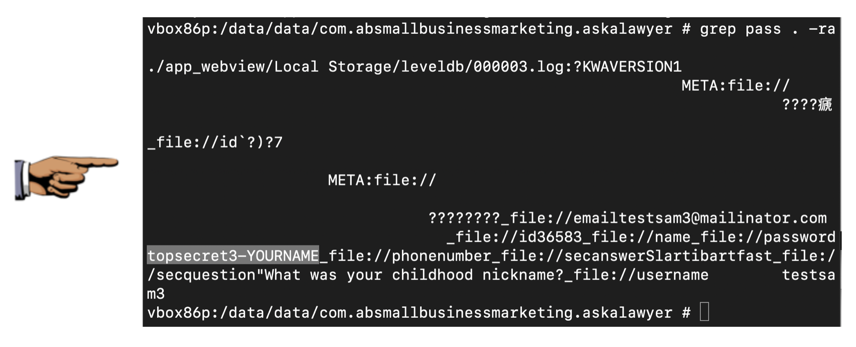
Capture a full-screen image.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
Save the image with the filename "YOUR NAME Proj 2x", replacing "YOUR NAME" with your real name.