python3 -m pip install sympy
How large are p and q? Well, they can't both be larger than the square root of n, or they'd be larger than n when multiplied together.
Start Python 3 in interactive mode with this command:
python3
import math
n = 10142789312725007
print(math.sqrt(n))
A good way to do this is to calculate n mod c, where c is a candidate. If c is a factor of n, the result will be zero.
We can test the first 20 candidates with a for loop.
Execute these commands:
c = 100711413
for i in range(c, c-40, -2):
print(i, n%i)
The third candidate is the winner, with a remainder of zero, as shown below.
Execute these commands:
p = 100711409
q = int(n / p)
print(p, q, n, p*q, n - p*q)
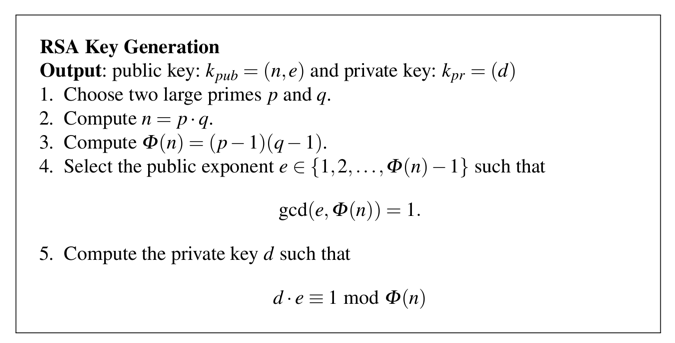
phin = (p-1) * (q-1)
print(p, q, n, phin)
(d * e) mod phin = 1d is the "multiplicative inverse" of e.
We know that e = 5 from the Problem Statement.
It's not obvious how to find d, but there's a simple way to do it in Python, using the "smpy" library.
In the Terminal window running python, execute these commands.
e = 5
import sympy
d = sympy.invert(e, phin)
print(d, e, d*e %phin)
Hi!
In the Terminal window running python, execute these commands.
x1 = ord('H')
x2 = ord('i')
x3 = ord('!')
x = x1*256*256 + x2*256 + x3
print(x)
Execute these commands:
y = x ** e % n
print(y)
Execute this command:
xx = y ** d % n
Press Ctrl+C to stop the computation.
To compute such a number, we must use the pow() function. Execute this command:
xx = pow(y, d, n)
Execute these commands to see the types:
print(type(y))
print(type(d))
print(type(n))
To fix it, we'll change it back to "int", and check that its value is unchanged.
dd = int(d)
print(d, dd)
print(type(dd))
Now execute these commands to decrypt the message:
xx = pow(y, dd, n)
print(xx)
x1 = int(xx / (256*256))
x2 = int((xx - 256*256*x1) / 256)
x3 = int(xx - 256*256*x1 - 256*x2)
msg = chr(x1) + chr(x2) + chr(x3)
print(x1, x2, x3, msg)
C 402.1: Encrypt "WOW" (10 pts)
Execute these commands to load the same keys used above:Using those keys, encrypt this message:n = 10142789312725007 p = 100711409 q = int(n / p) phin = (p-1) * (q-1) e = 5 import sympy d = sympy.invert(e, phin)Hint 1: The message, converted to a decimal number, is 7 digits long and ends in 43.WOWHint 2: The encrypted message is 16 digits long and ends in 66.
The flag is the encrypted message.
C 402.2: Encrypt "OBEY!" (10 pts)
Using the same keys, encrypt this message:Hint 1: The message, converted to a decimal number, is 12 digits long and ends in 41.OBEY!Hint 2: The encrypted message is 16 digits long and ends in 81.
The flag is the encrypted message.
C 402.3: Message to Cueball (15 pts)
Cueball's public key is:Meghan sends this message to Cueball. Decrypt it.(111036975342601848755221, 13)The flag is the decrypted message.80564890594461648564443
C 402.4: Message to Rob (15 pts)
Rob public key is:Meghan sends this message to Rob. Decrypt it.(1234592592962967901296297037045679133590224789902207663928489902170626521926687, 5557)Hint: Make square root calculations more precise.272495530567010327943798078794037733865151017104532777645776936985235709526002The flag is the decrypted message.
Prime Numbers Generator and Checker
Arbitrary precision of square roots