CAUTION
This project uses traffic captured from a real malware attack. It may set off virus scanners and possibly even infect old, unpatched Windows machines.Don't do this project on a real Windows machine in normal use. Use your Windows virtual machine instead.
In this case we are using a fairly old Windows malware sample, so it's OK to use a Mac or Linux machine.
Don't use a regular Windows machine for this project, especially one used for other work, such as company machine at a workplace. However, using Windows as the host for a virtual machine is fine.
https://www.malware-traffic-analysis.net/2017/12/23/index.html
On this page, click the 2017-12-23-traffic-analysis-exercise.pcap.zip link.
infected
On the File tab, click the "Choose file" button, as shown below.
Navigate to the 2017-12-23-traffic-analysis-exercise.pcap file you unzipped and double-click it.
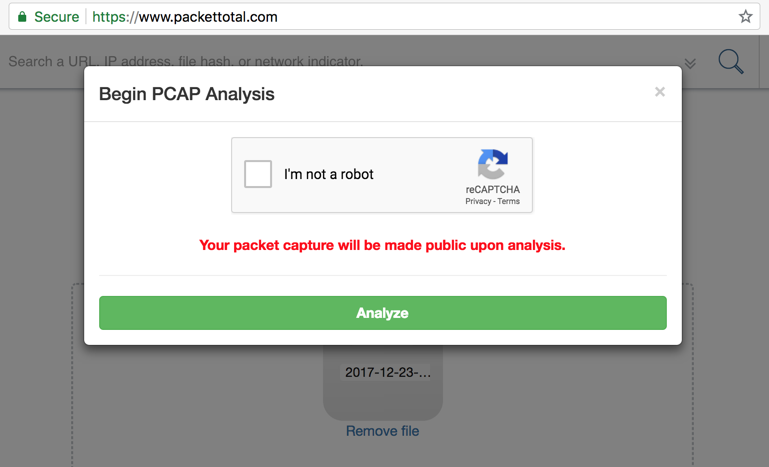
A "Begin PCAP Analysis" box pops up, as shown below, warning that the packet capture file will be made public after analysis.
That's a problem for real network data, but not for us, so check the box and click Analyze.
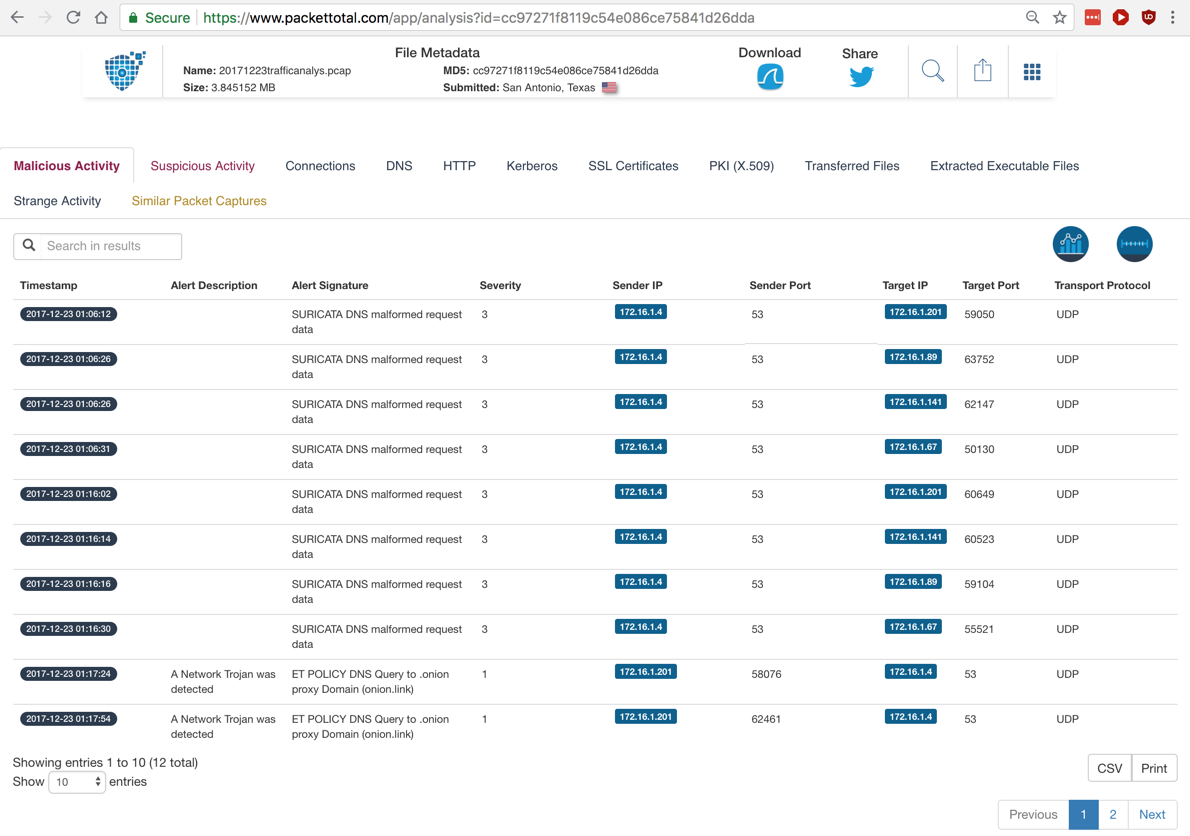
The first one may be malware traffic, but there's no further detail available here.
The second one indicates use of Tor, which is probably malicious activity also.
There are two alerts here too. The first one looks serious: a known malware hash value.
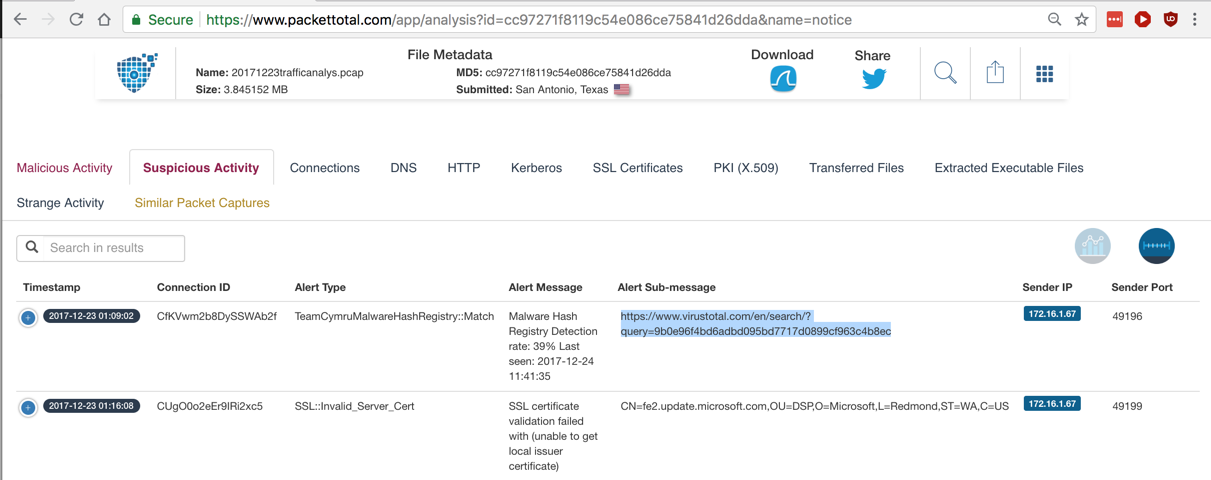
Highlight the VirusTotal URL from the alert, highlighted in the image below, copy it, and open that page.
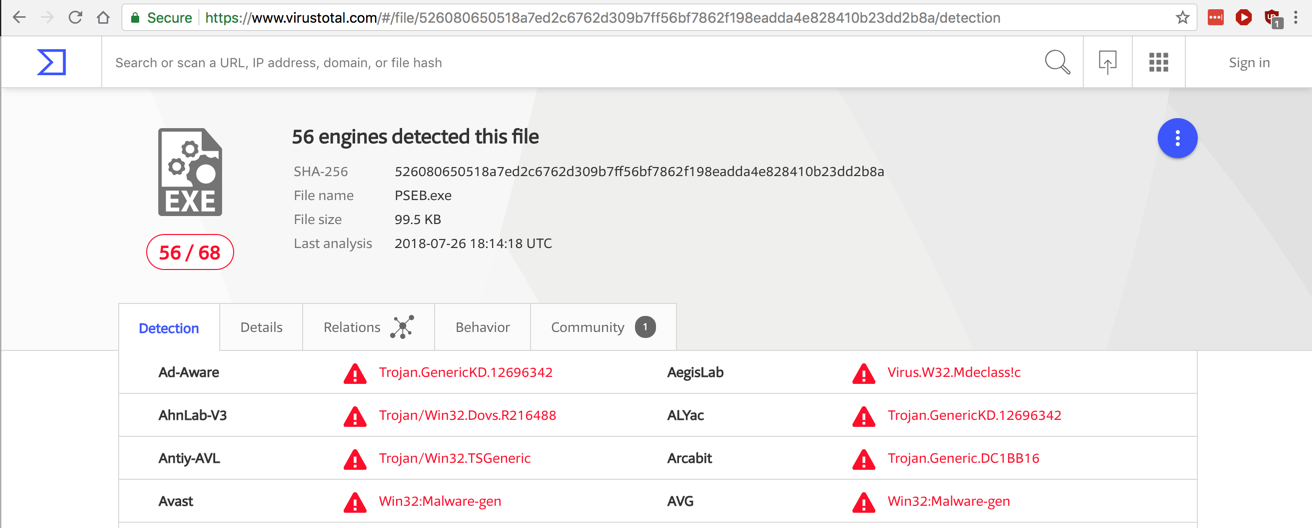
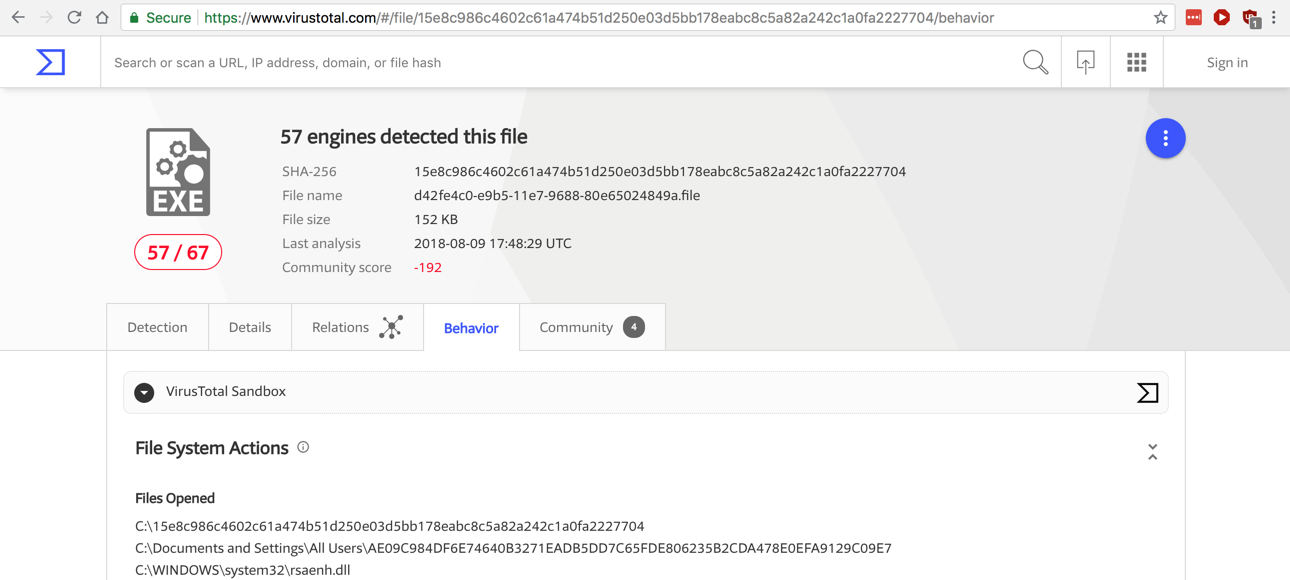
The file is detected as a Trojan, as shown below.
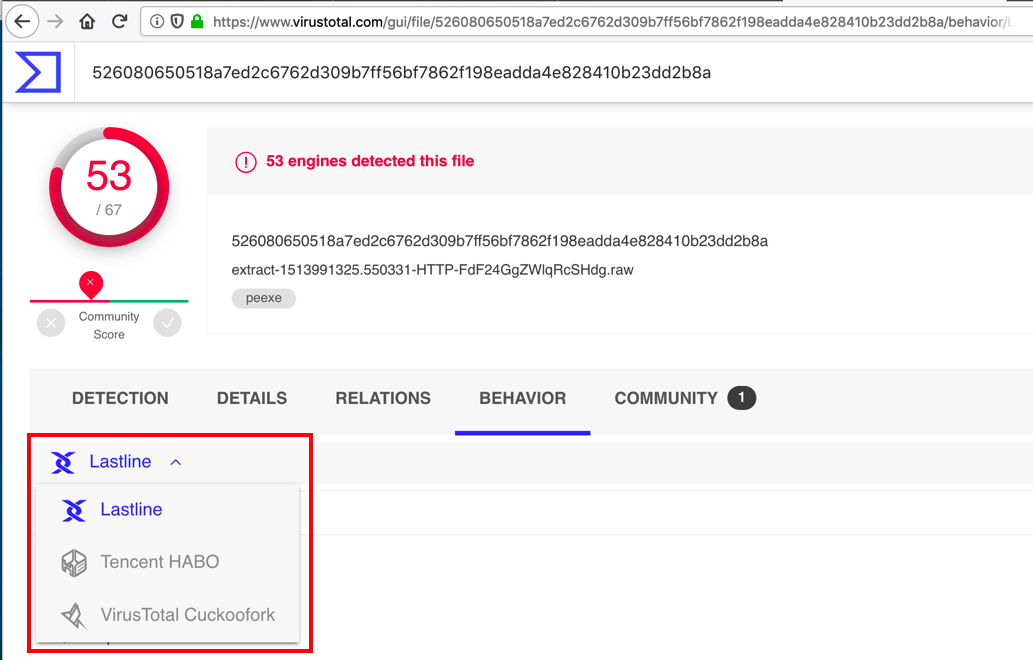
In VirusTotal, click the Behavior tab.
On the left side, under the word "DETECTION", click Lastline. There are three sandbox reports available, as outlined in red in the image below.
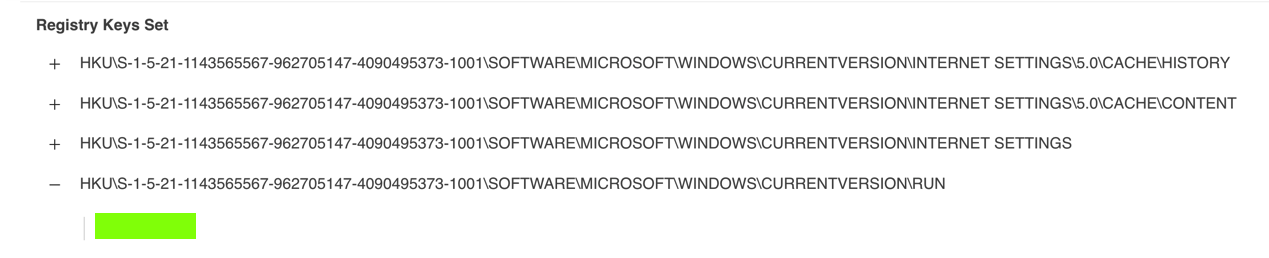
Find the registry Run key set by this malware, as shown below. The flag is covered by a green box in the image below.
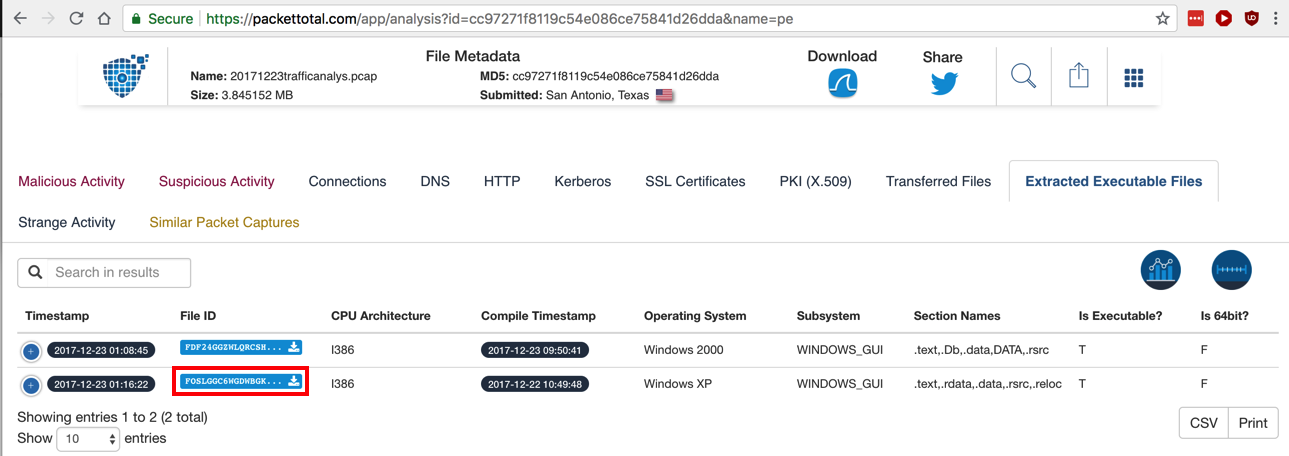
In the "File ID" column, click the little down-arrow on the right side of the second blue button (outlined in red in the image below) to download the Windows XP executable.
Check the box to verify that you are a human.
Click Verify.
Click "Download Potentially Malicious File".
A file downloads, named "extract-1513991782.382514-HTTP-FOSLGGC6wGdwbGkB3.raw".
Upload that file to VirusTotal.
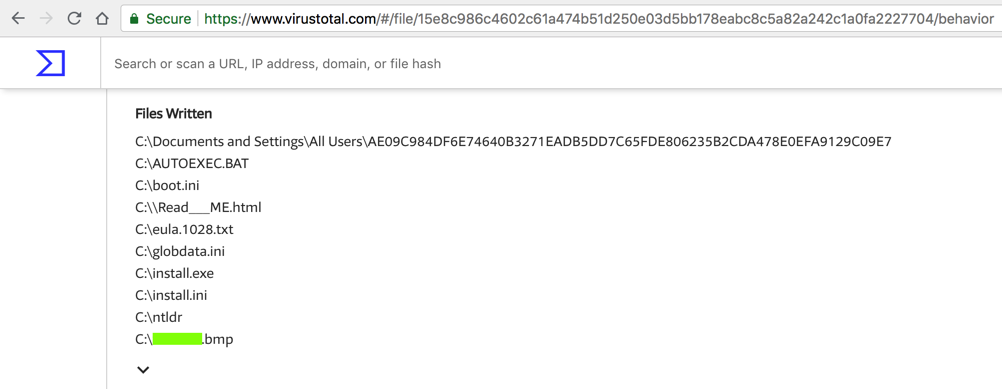
Examine its behavior in the sandboxes.
Download this file: IR305.3.zip
Unzip it with the password infected
Analyze it with tools of your choice. A file was downloaded from a server using port 443 for unencrypted traffic. What is the server's IP address? That's the flag.
What is that file's name? That's the flag.
Hint: one way to identify files is to install Git for Windows, run the "Git Bash" app, and use the "file" utility.
This malware creates a scheduled task in the C:\Windows\Tasks folder.
What is the name of that task? That's the flag.
Posted 9-17-18
Filename fixed 10-29-18
Ported to new flag system 10-3-19
Extra credit sections added 10-5-19
Hint added to flag 4 3-19-24