Here are details of the CERT test and notification, from 9/3/2014: Finding Android SSL Vulnerabilities with CERT Tapioca. This spreadsheet from CERT, shows "Android App SSL Failures": Android apps that fail to validate SSL
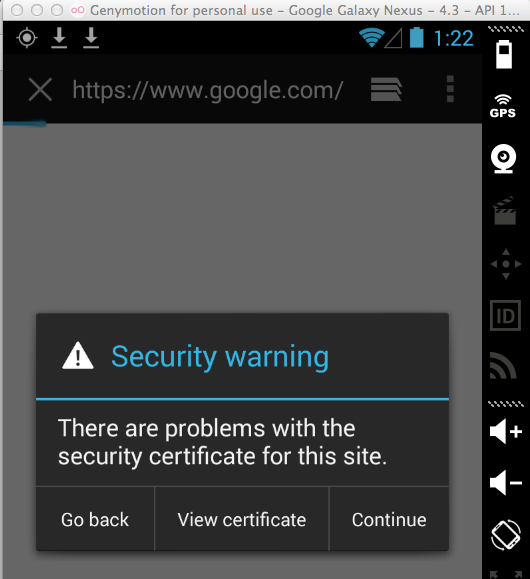
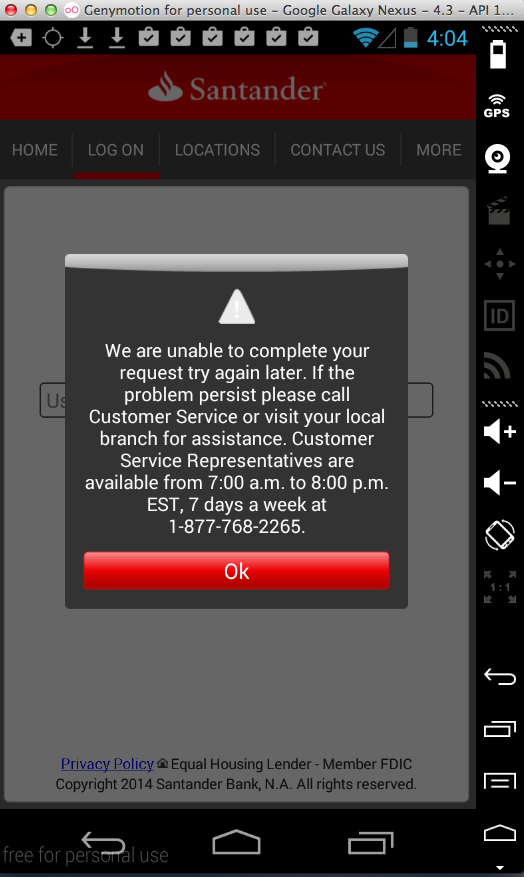
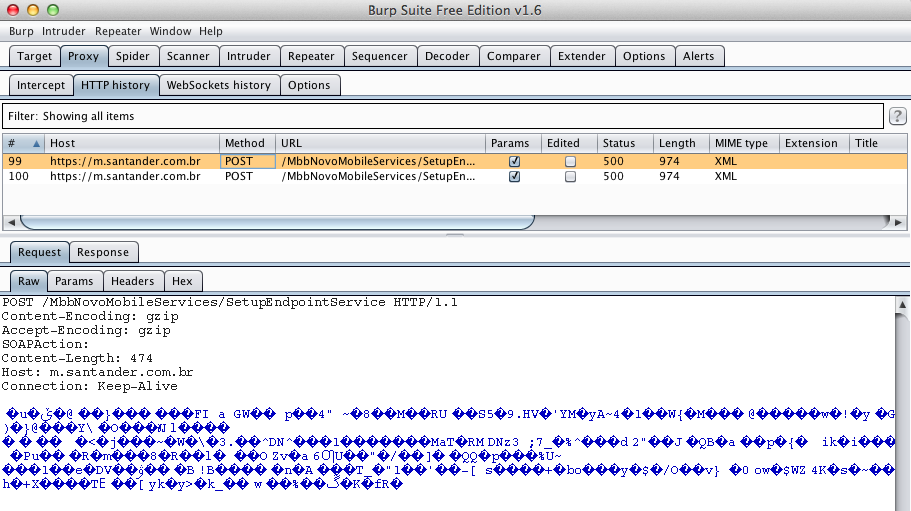
So no HTTPS connections should be possible through the proxy.
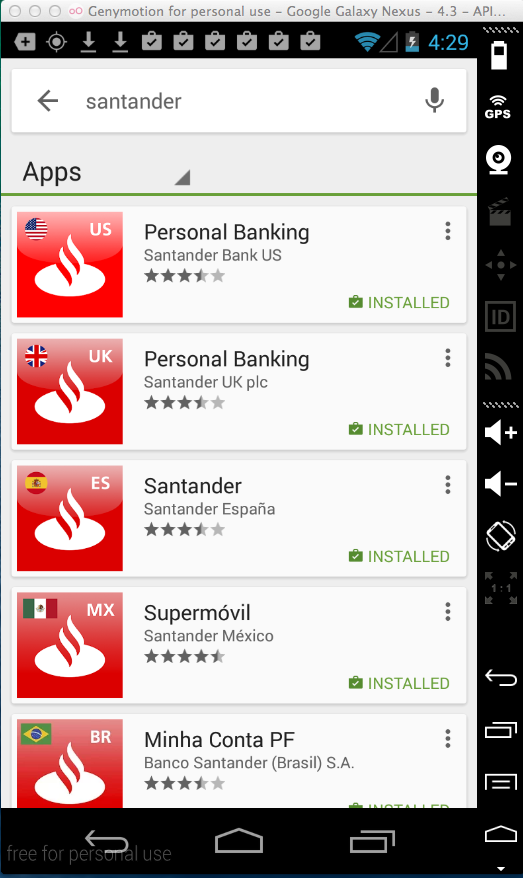
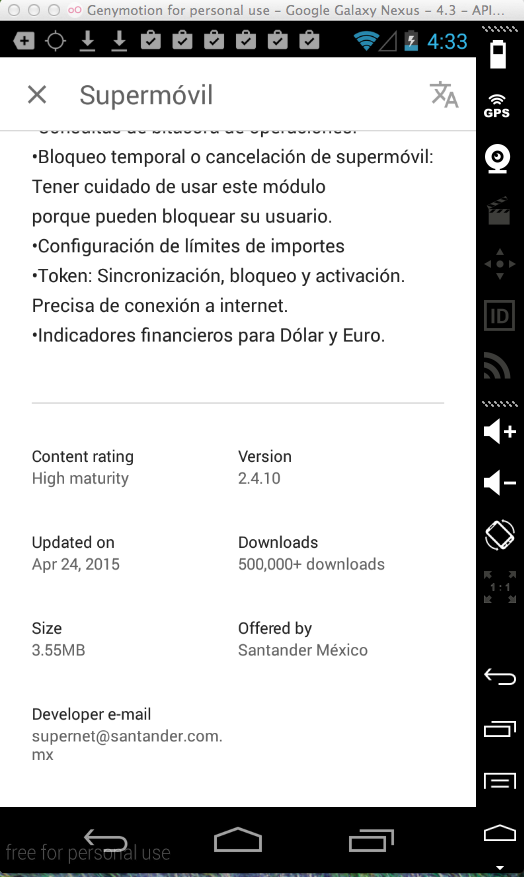
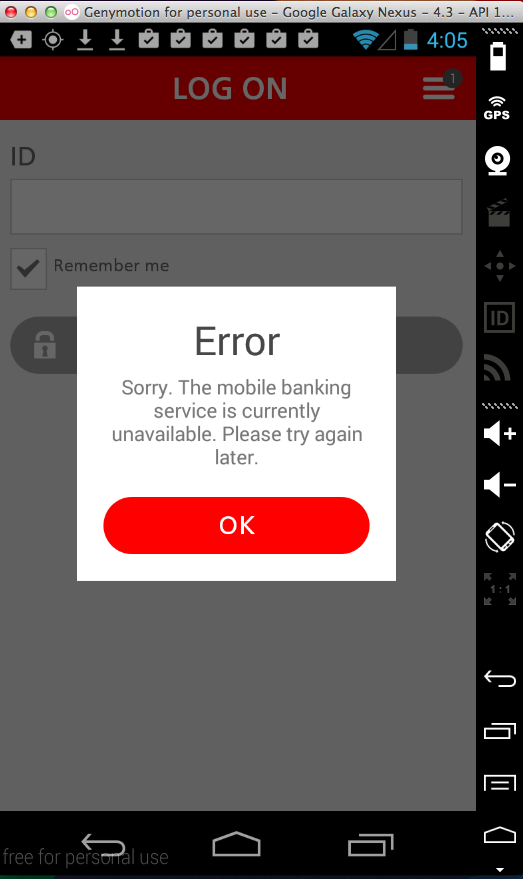
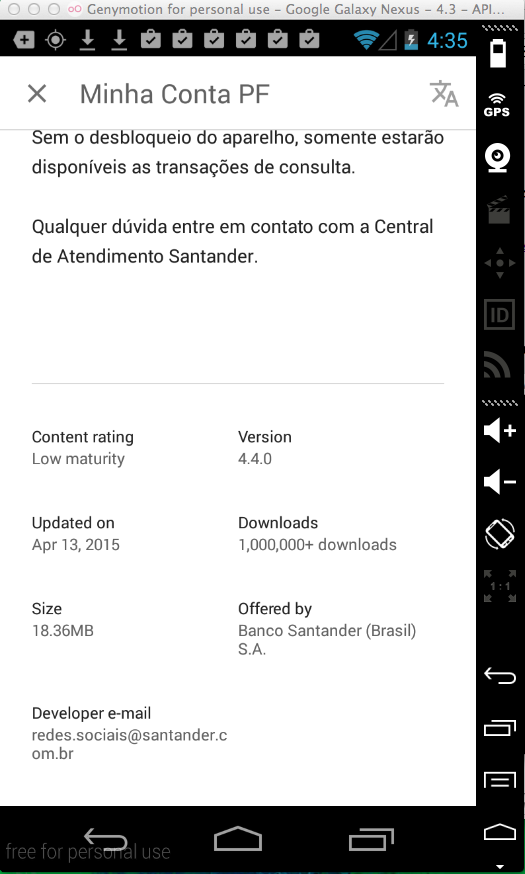
It was updated 4-24-15, but unfortunately it still doesn't implement HTTPS properly.
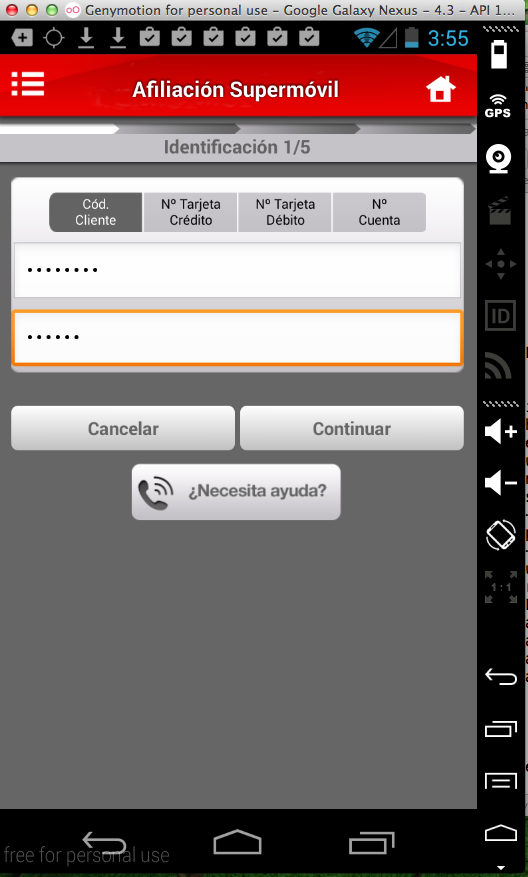
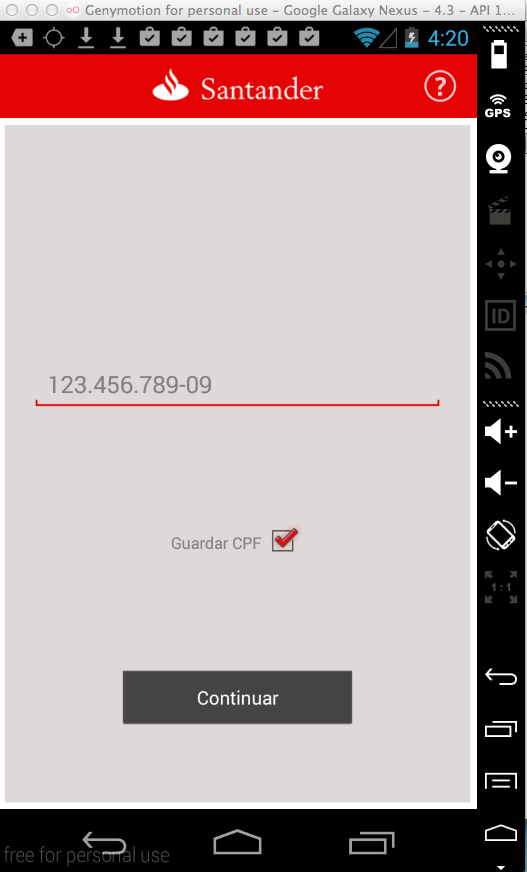
I entered test credentials into the app:
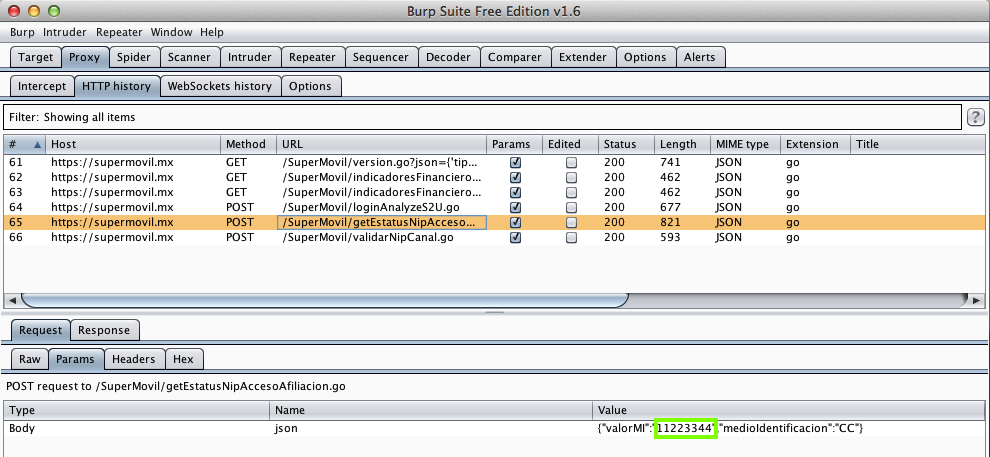
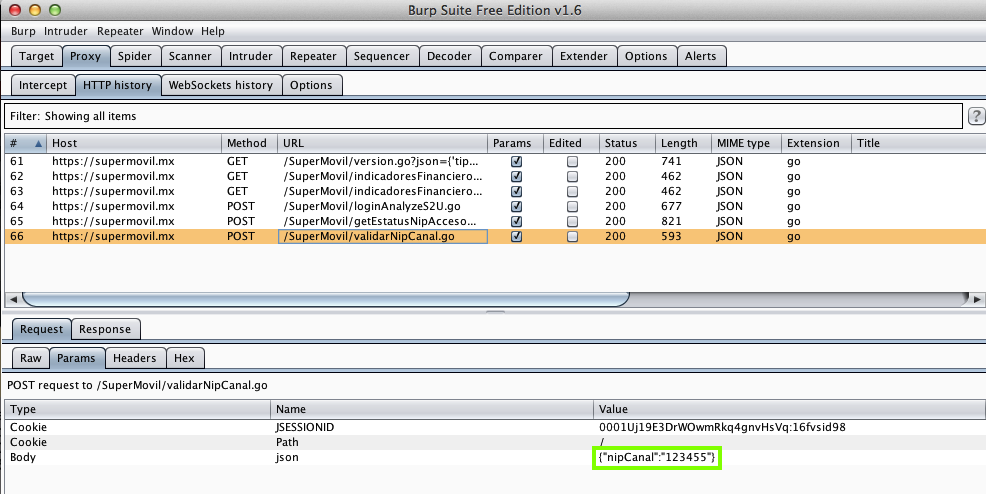
Here they are in two requests captured by the proxy, despite its lack of a trusted certificate:
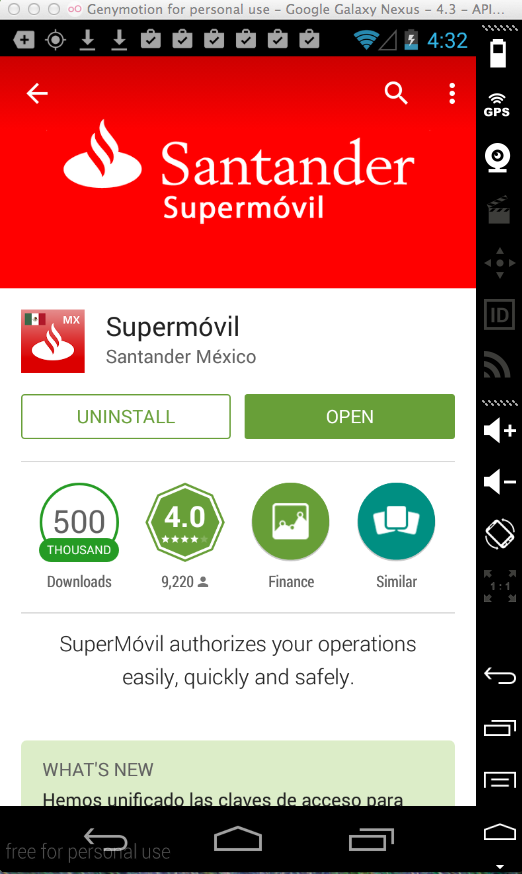
It was updated 4-13-15.
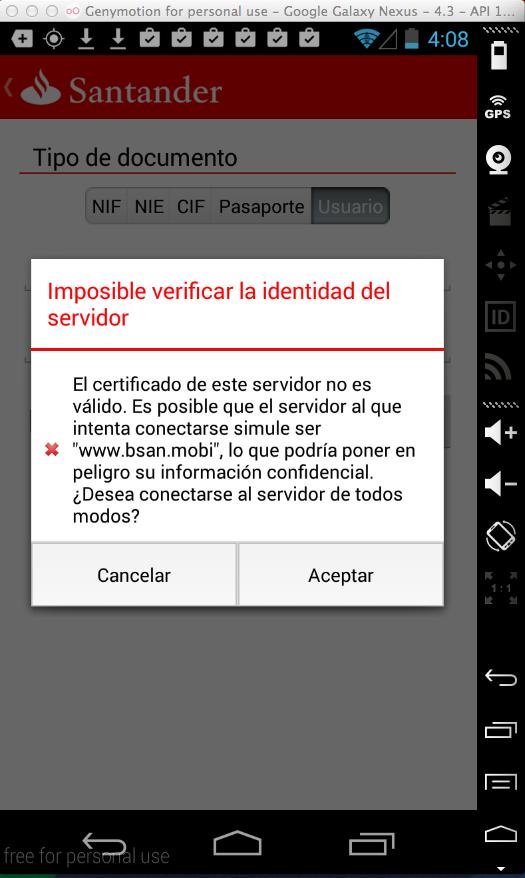
To test this, I needed a CPF number (like a US SSN). I found the algorithm here and a working example is 123.456.789-09.
When I sent that to the server, it sent an HTTPS GET with a lot of data in an incomprehensible binary format:
But I think that binary stuff contained the CPF number, because the Portuguese message I got:
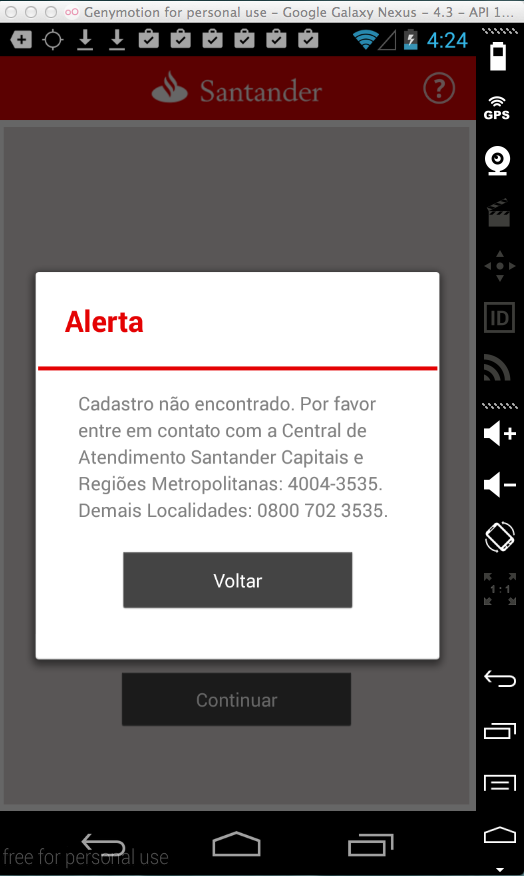
Translates to "Registration not found".
So it appears that the MITM attack works.